Steps to Enable a Remote Workforce with Workspace ONE - Part 1
Introduction
Based on the current events, many organizations are working around the clock to adapt and enable their employees to work remotely. This reality has caught many organizations by surprise. This blog provides guidance on how VMware can quickly help organizations enable remote work with VMware Workspace ONE.
VMware Workspace ONE is a platform that combines powerful integration across digital workspace solutions, including Access Management, Unified Endpoint Management (UEM), Analytics, Desktop and Application Virtualization and Endpoint Security. These are key solutions that enable remote work without compromising security and provides incredible user experience. Workspace ONE is organized into four core solutions:
- Workspace ONE UEM – Enables Unified Endpoint Management across Windows, Mac, iOS and Android devices, protecting corporate applications and data.
- Workspace ONE Access – Enables unified application catalog, providing a single place to secure access to all applications and single sign-on, in addition to streamlining communication with all users through Hub Services.
- VMware Horizon – Enables access to remote applications and desktops, keeping all data in the datacenter.
- Carbon Black Cloud – Cloud-native endpoint protection platform (EPP) that combines the intelligent system hardening and behavioral prevention needed to keep emerging threats at bay, using a single lightweight agent and an easy-to-use console.

Figure 1. Workspace ONE Platform
Step 1 – Accessing Workspace ONE in the Cloud
The immediate question is, “How do I get this solution up and running?” Organizations may have limited hardware and capacity, and most, if not all, employees must be remote. VMware can quickly provision a full Workspace ONE Cloud environment as SaaS, enabling quick access and scalability based on your organizations’ needs.
For Workspace ONE UEM and Workspace ONE Access, both are hosted as SaaS and infrastructure is managed by VMware. Your IT team will focus on the management of devices, applications, and security policies.
We have extended free trials of Workspace ONE for 90 days and 100 devices through July 31, 2020 available here!
For VMware Horizon, organizations can leverage Horizon Cloud Service to manage their cloud-hosted virtual desktops and applications, leveraging their capacity on Microsoft Azure or VMware Cloud on AWS. For more information, visit Maintaining Business Continuity in Challenging Times - Part-1.
For VMware Horizon, organizations can leverage Horizon Cloud Service to manage their cloud-hosted virtual desktops and applications, leveraging their capacity on Microsoft Azure or VMware Cloud on AWS. For more information, visit Maintaining Business Continuity in Challenging Times – Part-1.
Step 2 – User Directory Integration and Access to Corporate Resources
A minimum level of integration will be required, starting with Active Directory as the source to identify users on the organizations and permission access. Workspace ONE provides connectors that can be installed on-premises to achieve that integration and synchronize users and groups with Workspace ONE. This integration is the minimum required to unlock secure access to applications, and conditional access based on device posture, identity and user behavior. It also brings a unified catalog to the end user so they can access all applications from a single place, across all devices.
Access to corporate data hosted on-premises is another essential need as part of working remotely. Employees might need access to files, e-mails and applications that are seated on the internal network. In this case, IT must enable external access to employees without compromising security. Workspace ONE provides a security gateway appliance (Unified Access Gateway) that is deployed on the DMZ and enables secure access to those resources while ensuring every access is authenticated and from a managed device by the organization. A single Unified Access Gateway appliance can handle multiple use cases and thousands of users.

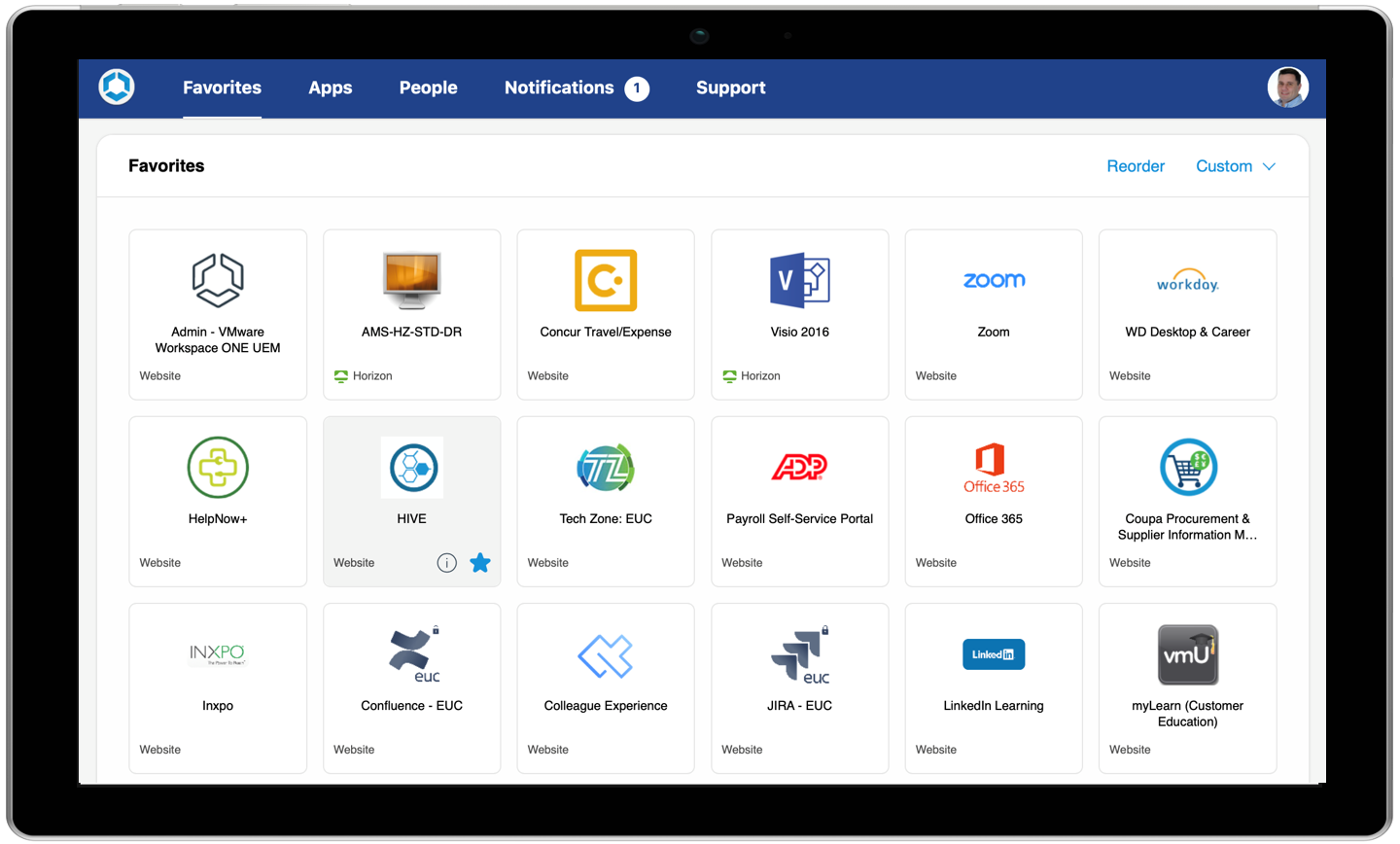
Figure 2. End-user experience accessing web, native and remote applications through the Unified Application Catalog
The Unified Application Catalog as part of Workspace ONE Intelligent HUB provides the seamless integration that enables employees to access their corporate applications like Service Now, Salesforce, Slack, Office 365, remote desktops and applications, bringing single sign-on and multi-factor authentication (MFA) to enhance security when accessing applications.
Step 3 – Defining Access Policies and Deploying Apps
A clear understanding of organizational needs to enable employees’ remote work drives the solution implementation and access policies. The employee’s roles and device types (corporate or BYOD) must be considered as part of this step, as this drives how security policies are applied to each, as well as how applications are delivered.
From the application perspective, it is important to plan what applications and how those will be available to end users. Workspace ONE can deliver and manage native and web applications that are integrated with security policies on the device. Workspace ONE also enables access to remote desktop and applications that run and maintain the data always on the data center.
From the device perspective, a group of users will continue using their corporate laptops and phones as part of their remote work life, which allows the Workspace ONE UEM administrator to have more granular controls of the physical device. This allows admins to apply security policies and restricting end-users’ access to device configuration. This scenario enables the end-user access to web and native applications from their device, combining security policies to protect the corporate data on the device. If the employee loses the device, a remote wipe can be issued to remove all corporate data from the device, or a full reset can be performed as well.
On the other side, a group of users will work from their personal devices, which limits the UEM administrator control of the physical devices. The organization will have to balance between physical applications deployed on the device vs. access to remote desktop (VDI) and applications. With Workspace ONE, the two options can seamlessly work together, achieving the balance between employee access and IT Security.
Step 4 – Onboarding your Users’ Devices
Depending on your industry or current situation, employees may or may not have a dedicated corporate device. First, you want to consider which device platforms or form factors each working group requires to be productive on their first days of working remotely. Your highly mobile users (those who already work from home or own a corporate device) will likely not require anything else other than an added management layer to reap some of the benefits of device management:
- Seamless access to any app from any device
- Ability to send real-time notifications to all employees to all their devices
- Over-the-air device configurations, policies, corporate baseline
- Visibility into your entire device fleet using custom dashboards and reporting
- Ability to secure all endpoints with a minimum standards baseline, deploying security solutions and policies, and real-time compliance checks with remediation actions
- Ability to enable end-users on What Is Workspace ONE, along with mitigating privacy concerns with the Privacy App
For users without a corporate device or for those who have never worked from home, communicating tips for working remotely is the best place to start. Along with that communication, you can enable them to onboard any device type (BYOD) they are comfortable working with or can get their hands on. You can send them an onboarding link, which will help them get started quickly. To help with this process, we have a campaign-in-a-box that includes pre-made, customizable templates, best practices and ideas to launch your own integrated campaign and start driving adoption with the Workspace ONE platform immediately.
From a technical perspective, after you have completed the Workspace ONE setup requirements, the quickest way to onboard existing devices is by having users go to getwsone.com or getws1.com and following the instructions to get started. Keep in mind there are streamlined onboarding methods; however, they might require some prerequisites or additional configurations. A few examples include OOBE/Autopilot for Windows, Dell Factory Provisioning, Apple Business Manager automated enrollment for macOS and iOS or Work Managed Device/Work Profile enrollment methods for Android. For more details, you can check out the quick-start learning paths on Tech Zone.

Figure 3. Unified Management for any OS and Any Device Type
Step 5 – Monitor Employee Experience & Provide Continuous Support
Now that you have everything configured and have begun to onboard new users and their devices, you might be thinking, “How the heck do I support these users?” If your support team has multiple members who are specialized, you can configure custom admin roles (or use one of the many pre-built admin roles) so that each admin only sees and has access to what is important to them. End users also have the ability to self-service many of their technical needs, such as being able to retrieve their BitLocker recovery key, locate their device or optionally wipe/lock-down the device if it becomes lost or stolen. Additionally, the help desk can quickly remotely view, control, whiteboard, record, view processes and share or grab logs from devices with the consent of users who need a higher level of assistance using Workspace ONE Assist.
The previous segments cover reactively supporting users. However, to increase your bandwidth, you can unlock the power of automation to focus on proactively helping users. Leveraging Workspace ONE Intelligence, along with various supported third-party integrations, you can achieve granular level custom dashboards, reports and robust automated actions. Keep devices secure and up to date with CVE ingestion and automatic patching of devices. Proactively send end-users replacement laptop batteries to replace degraded batteries that cannot hold a charge. You can even leverage Sensors (custom attributes) to key your automated actions based on any values obtained from your managed devices.
Our intent with this blog was to get you to start thinking about the high-level steps required to remotely deliver any app to any device, enabling workforces of all kinds to work from anywhere, instantly, while safeguarding sensitive information. Be sure to check out the Digital Workspace Tech Zone podcasts, Maintaining Business Continuity in Difficult Times – Part 1, where we discuss this topic in more detail with the experts from the EUC Technical Marketing team!
I would like to recognize the assistance and contributions provided by Josue Negron, EUC Staff Architect, End User Computing, VMware.
