VMware Compliance with the 14 NCSC Cloud Security Principles
Introduction
The UK National Cyber Security Centre (NCSC) guidance for the 14 Cloud Security Principles describes a comprehensive cloud information security program to help enable organizations meet compliance and security obligations within the UK. VMware has also participated in the UK Government G-Cloud initiative to ease cloud computing procurement by public-sector entities within the UK government: Refer to the VMware Workspace ONE listings on the UK Digital Marketplace for additional information.
Workspace ONE UEM, Workspace ONE Access, Workspace ONE Intelligence, and Workspace ONE Assist have undergone Service Organization Control (SOC) 2 Type 2 audits; have achieved International Standards Organization (ISO) 27001, 27017, and 27018 certifications; and have achieved the Cyber Essentials Plus certification. Additionally, Workspace ONE Access and Hub Services and Workspace ONE Intelligence are PCI-DSS certified. For the most up-to-date list of product audits and certifications, navigate to the VMware Trust Center. SOC 2 Type 2 reports are available under an NDA with VMware. VMware also publishes extensive documentation to familiarize organizations with our products and services on VMware Docs and VMware Tech Zone. Refer to the Cloud Services Guide on the VMware ONE Contract Center for detailed descriptions of service components, as well as shared service administration responsibilities between VMware and the customer.
Note: You can find the definitions for acronyms used throughout this document in: Acronyms used in the Workspace ONE Security Series.
Purpose
This document addresses the VMware enterprise Information Security Program, as well as policies and procedures in relation to the NCSC guidance for the 14 Cloud Security Principles for the following End-User Computing (EUC) cloud-hosted services: VMware Workspace ONE Unified Endpoint Management (UEM), Workspace ONE Access, Workspace ONE Intelligence, and Workspace ONE Assist. The Workspace ONE Access cloud environment also hosts data for Workspace ONE Hub Services. Within this whitepaper, these services are collectively referred to as “Workspace ONE.”
Audience
This document is intended for Workspace ONE commercial cloud administrators. It assumes at least intermediate knowledge of Workspace ONE cloud services, and focuses on the policies, processes, and controls supporting the cloud-delivered services. Federal Risk and Authorization Management Program (FedRAMP), on-premises, and third-party offerings are not in-scope for this document.
1. Data-in-Transit protection
Table 1: NCSC Guidance for protection for Data-in-Transit
| NCSC Guidance | |
| Principle | User data transiting networks should be adequately protected against tampering and eavesdropping. This should be achieved through a combination of: network protection - denying your attacker the ability to intercept data encryption - denying your attacker the ability to read data |
| Goals | You should be sufficiently confident that:
|
In alignment with PCI-DSS, Workspace ONE cloud applications enforce TLS encryption in transit to and from the VMware cloud environments over the public Internet to protect data against man-in-the-middle attacks: In transit encryption includes traffic between end user devices and service, the service and other services (i.e., on-premises connectors, customer systems), and internally within the service, where applicable. Firewalls, managed perimeter devices, and strong physical and logical access controls provide layered security within all Workspace ONE cloud environments.
Between Users and the Service
Message-level encryption secures all traffic traversing public networks and any sensitive interactions between Workspace ONE nodes (Workspace ONE and its integration components) and the user endpoints. These message-level interactions are encrypted with 2048-bit RSA asymmetric keys using digital certificates. Furthermore, HSTS headers in the Workspace ONE administrative consoles ensure that clients connect to the application over TLS/SSL after initial connection. Workspace ONE service web servers only support TLS 1.2 or higher.
Between Service Components
Workspace ONE supports integration with various customer enterprise systems to extend customer service investment: Integration with existing customer systems may require on-premises connectors. VMware publishes clear decision points and design considerations for these limited server requirements.
Note: Workspace ONE integration, service administration, recommendations and troubleshooting information is published on VMware Docs, VMware Tech Zone, My Workspace ONE Portal, and VMware Knowledgebase.
Integration between Workspace ONE platform components (Workspace ONE UEM, Workspace ONE Access, and/or Workspace ONE Intelligence) is performed securely through API integration and/or on-premises connectors. REST API calls take place over HTTPS with a certificate signed by a publicly trusted Certificate Authority (CA). Workspace ONE can securely integrate with on-premises services, such as Active Directory (AD), through connectors which proxy data to the cloud using HTTPS (TLS).
Internally Within the Service
To help ensure the availability of our services, VMware replicates primary production environment data to backup locations for quick service restoration in the unlikely event of a disaster. Data is encrypted in transit between primary and backup locations.
VMware Access to Production Environments
Access to the production environment is secured through a combination of VPN, IP address allow listing or jump servers using MFA and AD credentials. Production environment access is monitored and logged. In alignment with PCI-DSS, system sessions are set to an idle timeout of 15 minutes. Quarterly User Access Reviews are conducted to review privileged access and to remove/deactivate accounts with 90 days of inactivity. Note that customers manage Workspace ONE through web-based consoles and do not directly manage cloud environments.
2. Asset protection and resilience
Table 2: NCSC Guidance for asset protection and resilience
| NCSC Guidance | |
| Principle | User data, and the assets storing or processing it, should be protected against physical tampering, loss, damage or seizure. |
| Considerations | The aspects to consider are:
|
VMware models our Asset Management program after ISO 27001 and NIST 800-53 standards. We partner with Amazon Web Services (AWS) to host Workspace ONE cloud environments in the UK. We also partner with VMware Cloud on AWS (VMC on AWS) to host Workspace ONE UEM. AWS, and VMC on AWS have undergone SOC 2 Type 2 audits and has achieved at least PCI-DSS and ISO 27001 in addition to ISO 27017 and 27018 certifications. As part of our vendor risk management program, VMware validates security controls in the SOC reports and certificates for our data centers partners; appropriate agreements and service level agreements (SLAs) are in place. The asset inventory is regularly reviewed in accordance with PCI-DSS requirements.
Note: AWS publishes compliance and security information for their services. Reports and attestations can be acquired directly from these providers.
Workspace ONE UEM, Workspace ONE Access, Workspace ONE Intelligence, and Workspace ONE Assist have undergone SOC 2 Type 2 audits; have achieved ISO 27001, 27017, and 27018 certifications; and have achieved the Cyber Essentials Plus certification. Additionally, Workspace ONE Access and Hub Services, and Workspace ONE Intelligence are PCI-DSS certified. For the most up-to-date list of product audits and certifications, navigate to the VMware Trust Center.
2.1 Physical Location and Legal Jurisdiction
Table 3: NCSC Guidance for physical location and legal jurisdiction
| NCSC Guidance | |
| Principle | In order to understand the legal circumstances under which your data could be accessed without your consent, you must identify the locations at which it is stored, processed, and managed. You will also need to understand how data-handling controls within the service are enforced, relative to UK legislation. Inappropriate protection of user data could result in legal and regulatory sanction, or reputational damage. |
| Goals | You should understand:
|
Storage and Processing Locations
VMware clearly defines data storage, processing, and management locations for each of the Workspace ONE Cloud environments. Workspace ONE cloud delivered services are available in primary and backup locations hosted in the UK to meet our customers’ data sovereignty needs. Per standard terms in the VMware General Terms, the legal jurisdiction if the contracting entity is outside of the US is governed by the laws of Ireland.
Table 4: Data center locations by service
| Data Center Locations by service | |
| Workspace ONE UEM | Primary – UK Backup – UK |
| Workspace ONE Access | Primary – UK Backup – UK |
| Workspace ONE Intelligence | Primary – UK Backup – UK |
| Workspace ONE Assist | Primary – UK Backup – UK |
Additional processing locations for optional feature sets, e.g., Email Notification Service (ENS), are defined in the service Sub-processors Addendums.
Note: Workspace ONE services and ancillary service sub-processors are outlined in the sub-processor lists.
VMware Support Locations
VMware global Support Services team operates in a follow-the-sun model from locations in the UK, Ireland, US, Costa Rica, India, Japan, Australia, and Singapore. Support may be provided from any of these global offices or other locations as our support team continues to expand to meet customer requirements.
Privacy, the General Data Protection Regulations (GDPR) and Brexit
VMware complies with applicable obligations as a Data Processor. VMware enables customers to use services in a manner which enables the Customer to comply with applicable Data Protection Laws, including GDPR, as a Data Controller or as a Processor with respect to personal data. VMware has no direct relationship with the Users whose data it processes in connection with providing the Software and any related services. A User who seeks access, or who seeks to correct, amend, or delete inaccurate data should direct their query to the Customer. If the Customer requests VMware to modify or remove the data, we will respond to the Customer’s request in accordance with our agreement with the applicable Customer or as may otherwise be required by applicable law. As the Data Controller, Customers can export solution data at any time from the administrative console.
Note: VMware outlines security and privacy obligations in our standard cloud contracting terms which are available on the VMware ONE Contract Center.
VMware has completed the EU approval process for its global Binding Corporate Rules (BCRs) as a data processor. This significant regulatory approval allows VMware to use this transfer mechanism to protect the personal data of its customers when acting as their data processor. The BCRs apply to our customer data processing relationships. VMware’s application for Binding Corporate Rules in the UK (VMware's UK BCRs) is currently pending, and VMware’s Data Processing Addendum will be updated when the UK BCRs take effect. See this FAQ for more information and to address concerns regarding VMware's data transfer strategy in light of Brexit, and specifically the use of binding corporate rules (BCRs) and standard contractual clauses (SCCs).
Note: VMware is listed as a company for which the EU BCR cooperation procedure is closed. VMware also publishes BCR frequently asked questions (FAQs) for customer and partner review.
Workspace ONE administrators manage the data from the web-based consoles to help organizations to simplify data protection and privacy within a wider GDPR/UK GDPR compliance program:
- Access, update or remove data directly from the consoles at any time.
- Require terms of use (TOU) acceptance prior to end user allowing access to the service and enterprise resources: Users must accept the TOU before proceeding with enrollment, installing apps, or accessing the console. The Workspace ONE UEM console allows you to customize fully and assign a unique TOU to each organization group and child organization group. TOU acceptance can also be reviewed in the administrative console or VMware Intelligent Hub on end-user devices at any time.
- Export solution data at any time via CSV, as well as PDF and XLS formats.
- Workspace ONE Assist provides the ability to accept, pause, and end a remote session at any time, for enhanced privacy.
Scoped Data
Workspace ONE gives customers data minimization, accuracy, and audit controls to help administrators protect end-user data. Administrators can configure what data is collected from users and what collected data is viewable by admins within the Workspace ONE console. Use granular role-based access controls to restrict the depth of management information and features available to each administrative console user.
For an introduction to data collection by Workspace ONE service component, refer to the table below.
Table 5: Data collection by component
| Service | Data Collection |
| Workspace ONE UEM | Workspace ONE UEM data collects user and device data which is documented in the Workspace ONE Privacy Disclosure. Per platform data collection is outlined in the User Data Collection from BYOD End Users article on VMware Docs. |
| Workspace ONE Access | Workspace ONE Access minimally collects tenant configuration, username, first/last name, and email. Additional attributes may be collected as required by customer administrator. Please reference the Workspace ONE Privacy Disclosure for more information. |
| Workspace ONE Intelligence | Workspace ONE Intelligence consumes data from Workspace ONE UEM, Workspace ONE Access, Workspace ONE Intelligence for Consumer Apps, and customer-managed data sources. For a complete list of data collection points, please refer to the “Supported Data Categories by Integration” article available on VMware Docs. Please reference the Workspace ONE Privacy Disclosure for more information. |
| Workspace ONE Assist | Workspace ONE Assist collects limited device data required for remote device management such as OEM data, storage, RAM, battery health, WIFI data, Bluetooth data, and more. Workspace ONE Assist may also have file manager access that includes read and write access to the device file system based on the platform type and the permissions granted by the User. Please reference the Additional Data for Specialized VMware Mobile App Functionality section of the Workspace ONE UEM area in the Workspace ONE Privacy Disclosure for more information. |
Refer to the VMware Privacy Notice for additional information regarding data collection and use.
2.2 Data center security
Table 6: NCSC Guidance for data center security
| NCSC Guidance | |
| Principle | Locations used to provide cloud services need physical protection against unauthorized access, tampering, theft or reconfiguration of systems. Inadequate protections may result in the disclosure, alteration or loss of data. |
| Goals | You should be confident that the physical security measures employed by the provider are sufficient for your intended use of the service. |
As part of our vendor risk management program, VMware reviews SOC reports and ISO certificates for our data center partners, including AWS; appropriate agreements and service level agreements (SLAs) are in place. AWS does not have logical access to our customers’ hosted data.
AWS has undergone SOC 2 Type 2 audits and has achieved at least PCI-DSS and ISO 27001 in addition to ISO 27017 and 27018 certifications. AWS offers best-in-class physical security, including at ingress and egress points through 24/7/365 on-site monitoring, required badge access, mantraps, and so on.
Note: AWS publishes compliance and security information for their services. Reports and attestations can be acquired directly from AWS.
VMware leverages AWS Availability Zones for availability and data resiliency. Each data center facility is unique in its specific approach to the physical infrastructure, but AWS follows the same general principles for power redundancy and physical access controls.
Various power, cooling, and fire suppression measures, include redundant power to each component with dual power distribution unit (PDU) and power in each cabinet: N+1 PDU and a generator fuel system for power, N+1 cooling and fire detection with early warning tools and dual interlock pre-action sprinkler systems.
2.3 Data-at-Rest protection
Table 7: NCSC Guidance for Data-at-Rest protection
| NCSC Guidance | |
| Principle | To ensure data is not available to unauthorized parties with physical access to infrastructure, user data held within the service should be protected regardless of the storage media on which it’s held. Without appropriate measures in place, data may be inadvertently disclosed on discarded, lost or stolen media. |
| Goals | You should have sufficient confidence that storage media containing your data are protected from unauthorized access. |
VMware leverages AWS Availability Zones for availability and data resiliency. Each data center facility is unique in its specific approach to the physical infrastructure, but AWS follows the same general principles for power redundancy and physical access controls:
- Controlled access into the data center facility by a combination of badge access, biometrics, and mantraps
- 24/7 staffing and on-site security
- Monitored entry and exit points and key aisles via CCTV camera monitoring
- Various power, cooling, and fire suppression measures, including power to each component is redundant with dual PDU and power in each cabinet: N+1 PDU and a generator fuel system for power, N+1 cooling, and fire detection with early warning tools and dual interlock pre-action sprinkler systems.
VMware implements strong protection at rest for applicable data hosted within VMware cloud environments. Data protection per Workspace ONE service is as follows:
Table 8: NCSC Guidance for data protection at rest per Workspace ONE service
| Data Protection at Rest per Workspace ONE Service | |
| Workspace ONE UEM | All user data is encrypted at rest via volume encryption with a minimum level of AES-256 symmetric algorithm. Workspace ONE UEM also uses application-level encryption to secure data: certificate private keys, client cookie data, and tokens are stored within the database and protected with 256-bit AES symmetric encryption algorithm. Locally defined passwords are stored using PBKDF2 with a salt of at least 256 bits and a sufficiently large number of iterations. |
| Workspace ONE Access and Hub Services | Private keys and other data considered sensitive by the application are encrypted at rest using an AES 256-bit algorithm. Locally defined passwords are stored using PBKDF2 with a salt of at least 256 bits and a sufficiently large number of iterations. |
| Workspace ONE Intelligence | Workspace ONE Intelligence is a cloud service that provides deep insights, analytics, and automation for the entire digital workspace. As such, Workspace ONE Intelligence was built as a cloud-native service and uses a combination of AWS-managed and VMware-managed KMS keys for all encryption at rest across the solution datastores. Encryption keys are managed in alignment with PCI-DSS standards. Data is encrypted at rest using AES-256 with GCM. |
| Workspace ONE Assist | Data considered sensitive (i.e., product admin/service account password) is obfuscated by hashing. Furthermore, the database resides on an internal network and is only accessible by other servers in the private subnet. Backups of logs are also stored encrypted. Keys are stored securely on servers and cannot be exported. Access to keys is restricted to limited staff. |
2.4. Data sanitization
Table 9: NCSC Guidance for data sanitization
| NCSC Guidance | |
| Principle | The process of provisioning, migrating, and de-provisioning resources should not result in unauthorized access to user data. |
| Goals | You should be sufficiently confident that:
|
AWS manages hardware sanitization for the underlying systems supporting VMware cloud environments. VMware environments regularly overwrite or delete hosted customer data according to a defined schedule. The VMware Data Processing Addendum (Deletion of Data) and the VMware Cloud Services Guide govern data deletion for standard hosting agreements.
2.5 Equipment disposal
Table 10: NCSC Guidance for equipment disposal
| NCSC Guidance | |
| Principle | Once equipment used to deliver a service reaches the end of its useful life, it should be disposed of in a way which does not compromise the security of the service, or user data stored in the service. |
| Goals | You should be sufficiently confident that:
|
Workspace ONE cloud environments are hosted in AWS Availability Zones located in the UK. AWS manages the underlying hardware which supports the VMware-managed environments, including system maintenance and equipment disposal, as well as physical access credential lifecycles. AWS revokes access credentials for the physical hosting spaces as required per ISO 27001 guidelines. AWS media destruction and decommissioning procedures are NIST 800-88 Rev 1 compliant.
Note: AWS publishes compliance and security information for their services. Reports and attestations can be acquired directly from AWS.
2.6 Physical resilience and availability
Table 11: NCSC Guidance for physical resilience and availability
| NCSC Guidance | |
| Principle | Services have varying levels of resilience, which will affect their ability to operate normally in the event of failures, incidents or attacks. A service without guarantees of availability may become unavailable, potentially for prolonged periods, regardless of the impact on your business. |
| Goals | You should be sufficiently confident that the availability commitments of the service, including their ability to recover from outages, meets your business needs. |
VMware Business Continuity (BC) and DR strategies include data and hardware redundancy using AWS Availability Zones, network configuration redundancy and backups, and regular testing exercises. VMware maintains inventories of critical assets including asset ownership, and VMware maintains an inventory of critical supplier relationships.
Workspace ONE cloud environments meet strict requirements for high availability and redundancy. We eliminate any single point of failure through the use of resilient AWS Availability Zones.
- Workspace ONE cloud delivered services have guaranteed standard uptime SLAs of 99.9%.
Note: See the Service Level Agreement for VMware Workspace ONE® and VMware Horizon® Cloud Service for SLA definitions and coverage. - Workspace ONE cloud delivered services uptime status, planned maintenance, and historical incident data are displayed on a consolidated Status page.
3. Separation between users
Table 12: NCSC Guidance for separation between users
| NCSC Guidance | |
| Principle | A malicious or compromised user of the service should not be able to affect the service or data of another. |
| Goals | You:
|
Customer instances are isolated from each other using logical techniques.
- All Workspace ONE cloud services Shared SaaS tenant data isolated at the application layer using unique identifiers. Customers can only access data keyed to their tenant.
- Workspace ONE Managed Hosting Service provides version upgrade flexibility by leveraging a single-tenant instance of various components, such as databases, within the multitenant logical service. There is no guarantee of, or design for, dedicated systems or components.
VMware contracts with IaaS providers in a public hosting model to deliver the Workspace ONE cloud service environments. Workspace ONE services enforce TLS data encryption between cloud environments and service clients (such as web consoles, user endpoints) over the public Internet. VMware uses subnets to connect systems in different security domains. All traffic passes through firewalls before reaching proxy servers.
Access to VMware production environments is secured through a combination of VPN, IP address allow listing or jump servers using MFA and AD credentials. Production environment access is monitored and logged. Note that customers manage Workspace ONE through web-based consoles and do not directly manage cloud environments.
4. Governance framework
Table 13: NCSC Guidance for governance framework
| NCSC Guidance | |
| Principle | The service provider should have a security governance framework which coordinates and directs its management of the service and information within it. Any technical controls deployed outside of this framework will be fundamentally undermined. |
| Goals | You should have sufficient confidence that the service has a governance framework and processes which are appropriate for your intended use. Good governance will typically provide:
|
Information Security Management System (ISMS) Governance
The VMware ISMS leverages guidance from industry best practices and regulatory standards, including NIST SP 800-53, PCI-DSS, and ISO 27001. We maintain written ISMS, and we perform annual reviews and audits of the program to ensure the integrity of our hosted offering. Our ISMS considers the following objectives:
- The threats, vulnerabilities, and likelihood of occurrence identified by assessment of risks relative to the overall business strategy and objectives.
- The legal, statutory, regulatory, and contractual requirements that VMware and relevant and applicable partners, contractors and service providers must comply with; and
- The principles, objectives, and business requirements for information handling, processing, storing, communicating, and archiving developed by VMware to support its business operations.
VMware has designated the Chief Security Officer to oversee our ISMS. For comprehensive security through the organization, multiple groups within VMware have a role in establishing, maintaining, monitoring, and operating the security practices for the ISMS:
- Incident and Vulnerability Management
- Security Engineering and Security Operations
- Human Resource Security
- Legal
- Governance Risk and Compliance
Regulatory Governance
VMware continuously reviews laws and regulations to appropriately respond to the evolving legal and privacy landscapes. Our in-house legal department is involved in the establishment and review of privacy policies to review which privacy laws and regulations are applicable to the jurisdictions in which we operate.
VMware has appointed a DPO for purposes of the UK GDPR/ EU GDPR: The DPO’s role is to assist a company to monitor internal compliance, to inform and advise on the company’s data protection obligations, to provide advice regarding data protection impact assessments and to act as a contact point for data subjects and the supervisory authority.
The VMware Board of Directors sets high standards for its employees, officers, and directors. Implicit in this philosophy is the importance of sound corporate governance. It is the duty of our Board of Directors to serve as a prudent fiduciary for shareholders and to oversee the management of the business. To fulfill its responsibilities and to discharge its duty, the VMware Board of Directors follows the procedures and standards that are set forth in these guidelines. These guidelines are subject to modification from time to time as the Board of Directors deems appropriate in the best interests of the business or as required by applicable laws and regulations.
5. Operational security
Table 14: NCSC Guidance for operational security
| NCSC Guidance | |
| Principle | The service needs to be operated and managed securely in order to impede, detect or prevent attacks. Good operational security should not require complex, bureaucratic, time consuming or expensive processes. |
| Considerations | There are four elements to consider:
|
We consider configuration and change management, vulnerability management, protective monitoring, and incident management procedures in our ISMS. VMware strives towards operating and managing all Workspace ONE environments using a consistent ISMS framework: Workspace ONE UEM, Workspace ONE Access and Hub Services, Workspace ONE Intelligence, and Workspace ONE Assist are all ISO 27001/ISO 27017/ISO 27018 certified services. Third-party and internal assessors validate these processes at least annually under the VMware ISMS program. These audits are essential to the VMware continuous improvement programs.
Workspace ONE UEM, Workspace ONE Access, Workspace ONE Intelligence, and Workspace ONE Assist have undergone SOC 2 Type 2 audits; have achieved ISO 27001, 27017, and 27018 certifications; and have achieved the Cyber Essentials Plus certification. Additionally, Workspace ONE Access and Hub Services, and Workspace ONE Intelligence are PCI-DSS certified. For the most up-to-date list of product audits and certifications, navigate to the VMware Trust Center. SOC 2 Type 2 reports are available under an NDA with VMware.
5.1 Configuration and change management
Table 15: NCSC Guidance for configuration and change management
| NCSC Guidance | |
| Principle | You should have an accurate picture of the assets which make up the service, along with their configurations and dependencies. |
| Goals | You should have confidence that:
|
We maintain a formal configuration management policy based on industry best practices to harden the cloud environment; revisions and exceptions to the configuration management policy are processed through a documented change management policy to help ensure the confidentiality, integrity, and availability of our hosted offering.
Our change management policy defines controlled changes to configurations in our production environments; change processes include required approval, testing, implementation, and contingency plans. Changes undergo standard testing and validation processes, and if for any reason a change is unsuccessful or does not pass the required testing phases, our teams execute a fallback plan. Workspace ONE UEM, Workspace ONE Access, Workspace ONE Intelligence, and Workspace ONE Assist have achieved ISO 27001, 27017, and 27018 certifications. Workspace ONE Access and Workspace ONE Intelligence have achieved PCI-DSS.
AWS manages the underlying hardware asset registers, as well as configuration and change management procedures for Workspace ONE cloud environments according to ISO 27001, 27017, and 27018. AWS media destruction and decommissioning procedures are NIST 800-88 Rev 1 compliant.
Note: AWS publishes compliance and security information for their services. Reports and attestations can be acquired directly from AWS.
5.2 Vulnerability management
Table 16: NCSC Guidance for vulnerability management
| NCSC Guidance | |
| Principle | Service providers should have a management processes in place to identify, triage, and mitigate vulnerabilities. Services which don’t, will quickly become vulnerable to attack using publicly known methods and tools. See our guide on vulnerability management for more detail. |
| Goals | You should have confidence that:
|
VMware employs a rigorous Vulnerability Management program as part of the VMware Information Security Program. We follow guidance established in NIST SP 800-30 and PCI-DSS, and we conduct regular risk and vulnerability assessments to identify, assess, and remediate emerging threats. When potential vulnerabilities are discovered, we follow a documented procedure to prioritize and deploy necessary patches within the cloud environment. Remediation efforts are prioritized and applied against critical and high-risk issues.
VMware identifies vulnerabilities and threat-sources through subscribing to relevant mailing lists, conducting interviews with various members of the Cloud community, attending conferences, and mapping data to the business landscape. VMware-managed scanning tools are regularly updated to ensure quick detection of emerging threats.
Defined change management procedure help ensure patches are compatible with the production environment. Rollback plans captured as part of change management processes where required.
5.3 Protective monitoring
Table 17: NCSC Guidance for protective monitoring
| NCSC Guidance | |
| Principle | A service which does not effectively monitor for attack, misuse, and malfunction will be unlikely to detect attacks (both successful and unsuccessful). As a result, it will be unable to quickly respond to potential compromises of your environments and data. |
| Goals | You should have confidence that:
|
Workspace ONE cloud environments are secured with layered defenses, including but not limited to, access control mechanisms, firewalls, malware controls, auditing mechanisms, network controls. Intrusion Detection Systems (IDS) monitor network traffic, log suspicious activity, and alert on suspicious network activity within VMware cloud environments.
In alignment with PCI-DSS, file integrity monitoring is in place within Workspace ONE services to detect malicious behavior or changes in system files or libraries. In addition, Workspace ONE Access and Workspace ONE Intelligence uses the Amazon Web Application Firewall (WAF) which provides application layer protection against common web exploits.
VMware Cloud Operations monitor cloud environments 24/7 for alerts or suspicious activity. VMware follows the Fault, Configuration, Accounting, Performance, and Security (FCAPS) model to monitor the cloud environment and has configured the system to notify IT personnel if the central processing unit (CPU) utilization is too high, disk space limited, memory issues, key service failures, bandwidth utilization, power consumption, or other defined performance items. IaaS providers offer built-in security and monitoring controls.
If a security event is discovered, VMware has enabled full auditing capabilities on all environments to enable the reconstruction of security incidents and events. We have provided a description of incident response management for the following section, 5.4 Incident management, and audit capabilities in Principle 12. Audit information for users.
5.4 Incident management
Table 18: NCSC Guidance for incident management
| NCSC Guidance | |
| Principle | Unless carefully pre-planned incident management processes are in place, poor decisions are likely to be made when incidents do occur, potentially exacerbating the overall impact on users. |
| Goals | You should have confidence that:
|
The VMware Incident Response program plans and procedures are developed in alignment with ISO 27001 and PCI-DSS standards. For the purpose of security and incident management, VMware maintains contacts with industry bodies, risk and compliance organizations, local authorities and regulatory bodies. Points of contact are regularly updated to ensure direct compliance liaisons have been established and to be prepared for a forensic investigation requiring rapid engagement with law enforcement.
VMware requires staff to report information security events as quickly as possible per corporate policies. At a minimum, these situations include:
- Ineffective security controls or access violations
- Breach of information integrity, confidentiality or availability expectations
- Human errors
- Non-compliances with policies or guidelines
- Breach of physical security arrangements
- Uncontrolled system changes
- Malfunction of software or hardware.
Incident Management Plan
VMware follows a formal Incident Management Plan that is maintained as part of our overall Information Security Program. Incidents are reported to the appropriate Cloud Operations team for categorization and resolution; issues are escalated to senior management according to a pre-defined protocol. VMware tracks issue alerts, responses, and resolutions throughout completion: Incident response teams prepare postmortem report to internal stakeholders and our Information Security Governance Committee for review. VMware will notify the appropriate customer IT stakeholders. VMware uses email announcements to maintain open lines of communication between support staff and customers regarding change management events, incident events, and problem events.
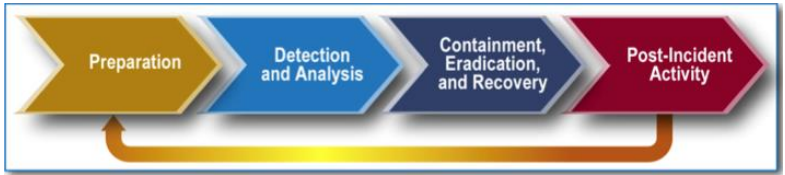
Figure 2: Incident Response Lifecycle
We periodically review incidents and update our incident response program as needed based on: Incident root cause and incident pattern analysis, as well as potential changes in the internal control environment and legislation. Incident response plans are tested at least once annually, whether a security incident has occurred or not.
- Results of the quarterly review are reported to management.
- Key metrics are defined, tracked, and reported to senior management on a yearly basis or as needed.
6. Personnel security
Table 19: NCSC Guidance for personnel security
| NCSC Guidance | |
| Principle | Where service provider personnel have access to your data and systems you need a high degree of confidence in their trustworthiness. Thorough screening, supported by adequate training, reduces the likelihood of accidental or malicious compromise by service provider personnel. |
| Goals | You should be confident that:
|
We maintain formal personnel security procedures as part of our Information Security Program, which includes comprehensive background checks. All employees acknowledge company policies and sign Non-Disclosure Agreement (NDA). Information security awareness training is mandatory; completion and end-of-course testing is recorded. Annual refreshers are required.
Background checks are performed in accordance with the VMware pre-employment background check protocols applicable to the region and are subject to local laws and regulations. As a general matter, VMware Human Resources (HR) Operations initiates and oversees the background check process. Results are treated as confidential personnel records, made available only to those outside HR Operations with a business reason to review or be consulted regarding the results.
Subject to applicable law, VMware, or its background check vendor, typically performs the following background checks:
- A verification of the applicant’s recent work history
- Confirmation of highest degree obtained, and professional qualifications required for the position
- Credit review for employees at the level of VP or higher in the Finance organization
- Review of certain criminal records, consistent with availability of records and limitations imposed by applicable law
All VMware employees are responsible for maintaining company sensitive information confidentiality, storing, and managing passwords appropriately, being aware of customer privacy concerns and remaining vigilant for security threats (such as social engineering, phone impersonations) always. Violations of VMware information security policies are subject to disciplinary proceedings, including termination and legal action, as necessary.
- VMware requires staff to report information security events as quickly as possible per corporate policies to help detect external threat actors or malicious insiders. At a minimum, these situations include:
- Ineffective security controls or access violations
- Breach of information integrity, confidentiality or availability expectations
- Human errors
- Non-compliances with policies or guidelines
- Breach of physical security arrangements
- Uncontrolled system changes
- Malfunction of software or hardware
- Bring your own (BYO) devices are not used to maintain the VMware cloud environment. VMware corporate-issued mobile devices are subject to automatic compliance policies that require and specify approved OS, patch and applications. BYO devices must be enrolled in Workspace ONE UEM to access VMware corporate information and are subject to additional corporate-mandated security controls.
- Access to VMware production environments is secured through a combination of VPN, IP address allow listing or jump servers using MFA and AD credentials. Production environment access is monitored and logged. Note that customers manage Workspace ONE through web-based consoles and do not directly manage cloud environments.
Initial and annual information security awareness is delivered through a Learning Management System (LMS). The LMS electronically records training proof of completion for employees. Cloud Operations personnel receive additional, specialized training as they assume job roles and responsibilities within 30 days of beginning work; training must be completed before authorizing access to VMware systems.
Note: Training completion tracking may differ depending on the training delivery type (i.e., instructor-led training or LMS).
Topics include:
|
|
Security Community
VMware has been an active participant in the broader software industry security community became an early BSIMM member in 2009 and has completed several reviews by BSIMM of our SDL. Findings are incorporated into our SDL to drive continuous improvements. VMware is a member of SAFECode, and we work closely with Security Analysts and Researchers and security organizations to stay current on the Industry threat landscape and security best practices. VMware Product Security VMware SDL is continuously assessed for its effectiveness at identifying risk and new techniques are added to SDL activities as they are developed and mature.
VMware is also active in the security research community and our security evangelism team works to actively cultivate relationships in the security community. VMware encourages continuous employee training programs which subsidize relevant conference tickets, such as BSides and BlackHat, training classes, and subscriptions to leading online training platforms for technical and business acumen. Additionally, VMware has job rotation programs designed to reignite and broaden employee work experience and retain top talent.
7. Secure development
Table 20: NCSC Guidance for secure development
| NCSC Guidance | |
| Principle | Services should be designed and developed to identify and mitigate threats to their security. Those which aren’t, may be vulnerable to security issues which could compromise your data, cause loss of service or enable other malicious activity. |
| Goals | You should be confident that:
|
We have developed Product Security Requirements to establish a security baseline for our products. These requirements are intended to guide teams through all stages of the Secure Software Development Lifecycle, from product inception and development to product testing. It also serves as a tool for senior management to benchmark product security against market expectations. Software testing include manual and automated testing methods. VMware has embedded security Subject Matter Experts (SMEs) in our R&D organization, as well as within Cloud Operations. Employees hold certifications such as CISSP, CISM, CIPM, CIPP/E, CCSP, CCDA, VCP, ITILv3, CNA, CompTIA A+, ISSA, CEH.
VMware follows a defined SDL which incorporates security into each phase (such as requirements, design, implementation, verification) of development. Our product security guidelines and security assessment framework incorporate multiple application frameworks and vulnerability sources, including the Open-Source Security Testing Methodology Manual (OSSTMM), the OWASP Testing Guide, OWASP Mobile Security Project, OWASP Top Ten, CWE/SANS Top 25. Code undergoes rigorous review by our Engineering and Development Security teams. The product suite undergoes multiple tests prior to release, including static and dynamic code reviews, penetration tests, fuzz and unit testing, attack surface reviews, and so on.
Workspace ONE code development is not outsourced. Code is primarily developed in-house, and we use some third-party and/or open-source code in our solution offerings. VMware performs open source and third-party (OSS/TP) software validation to safeguard against known vulnerabilities prior to being included in a VMware product release.
- VMware requires that its development teams use the latest, fixed versions of the OSS/TP software and publish the names and release levels of each OSS/TP product or library that the team uses in building VMware products or components.
- Code or products that VMware acquires undergo a formal testing and acquisition process: Contracts with suppliers address VMware information security requirements and any required risk remediation is evaluated prior to product acquisition.
Note: We publish pertinent information on the VMware Open-Source Disclosure page.
To securely deliver continuous product improvements, VMware has incorporated DevOps processes into our SDL where applicable. Continuous Delivery (CD) pipelines have logging enabled. Development teams can push code as a check-in and this process requires multiple code reviews in parallel with unit and integration testing. After successful completion of pass/fail tests, code is deployed into the VMware internal environment and then to UAT and hosted production environments.
VMware performs extensive penetration tests against our applications and services. The penetration tests are generally divided in three different phases, focusing on identifying high impact vulnerabilities which could lead to exploitation, theft of data, and overall privilege escalation. The tests typically follow a method intended to simulate real-word attack scenarios and threats that could critically impact the data privacy, integrity, and overall business reputation. Our third-party penetration testers hold numerous certifications ranging from OCSP to SANS certifications.
In alignment with PCI-DSS requirements, VMware encourages continuous employee training through annual training in up-to-date secure coding techniques, including how to avoid common coding vulnerabilities. VMware also subsidizes certification attempts (such as CISSP, CCSP), relevant conference passes, training classes, and subscriptions to leading online training platforms for enhancing technical and business acumen. Additionally, employees can participate in job rotation programs designed to reignite and broaden employee work experience. Refer to the VMware Product Security Whitepaper for additional information.
8. Supply chain security
Table 21: NCSC Guidance for supply chain security
| NCSC Guidance | |
| Principle | The service provider should ensure that its supply chain satisfactorily supports all the security principles which the service claims to implement. |
| Goals | You understand and accept:
|
VMware engages sub-processors to provide hosting services for the Workspace ONE cloud-delivered environments. We enter into agreements with our sub-processors to meet baseline security requirements and to adhere to applicable data protection laws. We work with reputable service providers and perform software validation for OSS/TP to safeguard against known vulnerabilities prior to incorporation within our products and services.
Workspace ONE cloud environments in the UK are deployed in AWS data centers. Sub-processors are outlined per service in the Sub-processors Addendums.
Note: Workspace ONE services and ancillary services sub-processors are outlined in the sub-processor lists.
We have also established compliance standards and service expectations with our data center providers and regularly audit data center controls, procedures, and independent assessments to assess and minimize service provider risk:
- SLAs are in place with our data center providers that stipulate baseline compliance standard and security requirements.
- We also review published SOC reports and PCI-DSS/ISO certifications, DR plans, and other applicable policies (such as access control policies, physical and environmental plans) of the processor.
- Additional information concerning data center sub-processors is outlined in Principle 2. Asset protection and resilience.
9. Secure user management
Table 22: NCSC Guidance for secure user management
| NCSC Guidance | |
| Principle | Your provider should make the tools available for you to securely manage your use of their service. Management interfaces and procedures are a vital part of the security barrier, preventing unauthorized access and alteration of your resources, applications and data. |
| Considerations | The aspects to consider are:
|
VMware shares the responsibility for securing Workspace ONE user management with customer or partner administrators.
- Workspace ONE customer administrators manage end-user and administrator accounts through the web consoles. Workspace ONE offers multiple authentication methods for console and end users, including two-factor and certificate-based authentication. VMware applications are subject to continuous testing to confirm control efficiency.
- VMware additionally implements strong access controls in accordance with role-based access control, separation of duties, and the principle of least privileges. Production environment access is secured through a combination of VPN, IP address allow listing or jump servers using MFA and AD credentials. System sessions are set to an idle timeout of 15 minutes. Logs are in place to review support staff access to all systems and environments. Quarterly User Access Reviews are conducted to review privileged access and to remove/deactivate accounts with 90 days of inactivity.
9.1 Authentication of users to management interfaces and support channels
VMware Internal Support Channels
VMware employees use an internal web ticketing system, dedicated support line, or self-service password tool to reset credentials. Users are verified prior to credential reset or temporary password delivery. Where temporary credentials are issued, users will be required to change passwords upon initial login. Cloud environment privileged credentials are reset and fully tracked through an internal ticketing system.
Customer Support Channels
To validate customer support requests, VMware assigns a unique 10-digit numeric identifier (Customer number) to each customer contact for the purpose of technical support. The customer number is created for users either when users create a VMware or VMware Customer Connect profile themselves, or when a new order is placed for users that do not have a VMware or VMware Customer Connect profile. Customer numbers are unique to individuals (similar to a personal identification number).
- Users can use their customer number to log in to VMware Customer Connect, file support requests through the interactive voice response system (IVR), or when working directly with a customer service representative. The customer number is displayed in their VMware Customer Connect profile and in support request forms.
- Customer numbers are unique for each customer contact (each individual who creates an account with us) and should not be shared with others.
Note: Refer to the VMware Tech Support Guide for additional information. Note that support for products and services licensed through partners may differ depending on the purchasing model.
9.2 Separation and access control within management interfaces
Customer Managed Users – Overview
Workspace ONE administrators can manage Workspace ONE from any web browser, anywhere in the world by simply logging into secure consoles. These consoles do not need to be downloaded, installed or configured, saving your IT department time and resources. Workspace ONE service portals may include:
- Workspace ONE My Apps Portal
- Workspace ONE Access Administrator Console
- Workspace ONE UEM Administrator Console
- Workspace ONE Intelligence Administrator Console
Workspace ONE administrative and end-user portals fully encrypt data in transmission with TLS over the public Internet.
The Workspace ONE UEM administrative console supports IP whitelisting for Managed Hosting environments. Workspace ONE Access administrators can define network ranges with IP addresses allowed for user logins to cloud applications: Assign these ranges when you apply access rules to Cloud applications.
Note: This functionality requires Workspace ONE UEM and Workspace ONE Access integration.
The Workspace ONE My Apps for end users delivers a seamless web based SSO experience on any device on any major browser. The Workspace ONE My Apps portal is also available as a native application on iOS, Android, and Windows. Workspace ONE UEM functionality can be delivered through Workspace ONE Intelligent Hub and productivity apps (VMware Boxer, Workspace ONE Content, Workspace ONE Web, Workspace ONE PIV-D Manager) are also available on mobile devices. Workspace ONE containers use AES 256-bit encryption for Data-at-Rest.
Note: Workspace ONE comes in several editions to make it simple for organizations to license the right amount of technology based on user and endpoint requirements. Refer to the complete feature comparison by edition under Compare for license inclusions.
Workspace ONE and the associated administrative portals undergo rigorous internal and third-party penetration and vulnerability assessments as a crucial step of our SDL. Issues, where uncovered, are tracked through remediation and prioritized according to criticality.
Customer Managed Users – Creation
Workspace ONE customer administrators can create locally defined users or integrate with AD/LDAP to inherit existing identity permission structures and credentials: Workspace ONE UEM integrates with Workspace ONE Access to extend existing directory infrastructure and provide a seamless Single Sign-On (SSO) experience to web, mobile, cloud, and legacy applications.
- Workspace ONE Access uses SAML 2.0 assertions to federate users. Workspace ONE can also eliminate the need to create user accounts in advance with just-in-time (JIT) provisioning: This functionality creates users on demand the first time they log in to Workspace ONE Access using single sign-on through a third-party Identity Provider (IdP).
Note: Available for tenants enabled with a third-party SAML identity provider such as ADFS, Ping Federate, or Google Apps. - Workspace ONE Intelligence and Workspace ONE Assist use the Workspace ONE UEM console for authentication. Workspace ONE Intelligence for Consumer Apps customers can access the administrative panel or through the Workspace ONE Intelligence console on cloud.vmware.com without an existing Workspace ONE deployment.
Note: Data for Workspace ONE Consumer Apps is also hosted in the Workspace ONE Intelligence service boundary.
Customer Managed Users – Role-based Access Controls
Each administrative console records activity and provides detailed application-level logs of the events or actions taking place. The solution maintains and displays this information to authorized users for auditing and reporting purposes.
Workspace ONE UEM administrative access is enforced by role-based access controls (RBAC): Customers can use built-in and custom roles to define the device groups that an IT administrator can access and manage within the console. Administrators can restrict the depth of device management information and features available to each console user. Workspace ONE Assist RBAC is enforced by Workspace ONE UEM controls.
- Customers can create additional administrator roles with different level of access in the management console. For example, you could create an administrator role that manages the application catalog resources but cannot entitle users to resources or create access policies.
Workspace ONE Access management portal includes RBAC with the following roles: Super administrators, Directory administrators, and Read-only administrators.
Workspace ONE Intelligence management pane also includes RBAC. Available administrator roles include Administrator, Analyst, Auditor, and Automator. Each role has specific permissions to offer quick assignment with appropriate access to Workspace ONE Intelligence features.
Administrators can access the Workspace ONE Access and Workspace ONE Intelligence management panes through the Workspace ONE UEM console. Navigate to VMware Docs for full descriptions of available pre-configured and customizable administrator roles across Workspace ONE platform.
10. Identity and authentication
Table 23: NCSC Guidance for identity and authentication
| NCSC Guidance | |
| Principle | All access to service interfaces should be constrained to authenticated and authorized individuals. Weak authentication to these interfaces may enable unauthorized access to your systems, resulting in the theft or modification of your data, changes to your service, or a denial of service. |
| Goals | You should:
|
VMware Authentication Policies
Production environment access is secured through a combination of VPN, IP address allow listing or jump servers using MFA and AD credentials. VMware manages strong password policies for access to production environments and corporate resources. VMware passwords are checked cryptographically (such as entropy calculations) for strength. Administrator passwords are changed every 90 days in alignment with PCI-DSS requirements.
Passwords:
- Cannot be from a dictionary word
- Cannot be a name
- Cannot be repeated over a given period
Customer Managed Authentication Policies
Workspace ONE controls access to mobile, web, cloud, Windows, Mac, Chrome, and virtual apps on a per-application basis. Workspace ONE examines authentication context such as authentication method, user group, target app, network location, and device state to automate access decisions and keep corporate data safe. Workspace ONE administrators can create locally defined users and can require strong password criteria for both administrators and end users and/or admins can integrate with AD/LDAP to inherit existing identity permission structures and existing credentials. Workspace ONE Access uses SAML 2.0 assertions to federate users with existing credentials. Workspace ONE Intelligence and Workspace ONE Assist use the Workspace ONE UEM console for authentication.
- Through tight integration between Workspace ONE UEM and Workspace ONE Access, Workspace ONE helps ensure that only the right devices get access to data with real-time, continuous device compliance checks. Workspace ONE ensures that managed devices comply with IT policies on rooted or jailbroken devices, whitelisted and blacklisted apps, open-in app restrictions, and other policies enforced through the policy engine.
- Workspace ONE UEM integrates directly with certificate authorities, public key infrastructure (PKI) or third-party providers to provision certificate profiles for various systems, including Wi-Fi, VPN, and Microsoft EAS, and can automatically distribute certificates to devices without user interaction.
Note: Workspace ONE integrates with various CAs: Refer to the Certificate Authority Integration Guide. Find additional information on VMware Docs. - Workspace ONE Access supports multiple authentication methods. Customers can configure a single authentication method and the solution can set up chained, two-factor authentication. Customers can also use an authentication method that is external for RADIUS and SAML protocols.
- Workspace ONE Access supports two-factor authentication for the Workspace ONE My Apps portal via a password and a VMware Verify passcode. Workspace ONE Access can also integrate with multi-factor authentication providers to deliver a range of mobile MFA features including push notification, TOTP code and SMS. The solution supports multi-factor authentication through Okta Verify, Duo, PingID, RADIUS, RSA SecurID, and RSA SecurID Access, RSA Adaptive Authentication, and certificate-based authentication.
On-premises Workspace ONE connectors support X.509v3 certificates for authentication with the VMware cloud. Workspace ONE UEM automatically deploys a unique X.509 certificate to enrolled devices when administrators whitelist applications for the VMware Tunnel: This certificate can then be used for mutual authentication and encryption between the application and the VMware Tunnel. Refer to VMware Docs for information regarding authentication policies.
11. External interface protection
Table 24: NCSC Guidance for external interface protection
| NCSC Guidance | |
| Principle | All external or less trusted interfaces of the service should be identified and appropriately defended. If some of the interfaces exposed are private (such as management interfaces) then the impact of compromise may be more significant. You can use different models to connect to cloud services which expose your enterprise systems to varying levels of risk. |
| Goals | You:
|
Workspace ONE enforces TLS data encryption between cloud environments and service clients (such as web consoles, user endpoints) over the public Internet. VMware uses Amazon VPC, security groups, and subnets to connect systems in different security domains. All external traffic passes through firewalls before reaching proxy servers.
Production environment access is secured through a combination of VPN, IP address allow listing or jump servers using MFA and AD credentials. Production environment access is monitored and logged. Note that customer administrators access and manage the Workspace ONE platform from web-based consoles and do not directly manage the cloud environment.
Service Authentication
Workspace ONE web interfaces and user endpoints are secured with TLS for Data-in-Transit. See Principle 9 and Principle 10 for an overview of service components and security. Note that customer administrators access and manage the Workspace ONE platform from web-based consoles and do not directly manage the cloud environment.
Continuous Testing
VMware performs extensive internal and external penetration tests at least annually. The penetration tests are generally divided in three different phases, focusing on identifying high impact vulnerabilities which could lead to exploitation, theft of data, and overall privilege escalation. The tests typically follow a method intended to simulate real-word attack scenarios and threats that could critically impact the data privacy, integrity, and overall business reputation.
12. Secure service administration
Table 25: NCSC Guidance for secure service administration
| NCSC Guidance | |
| Principle | Systems used for administration of a cloud service will have highly privileged access to that service. Their compromise would have significant impact, including the means to bypass security controls and steal or manipulate large volumes of data. |
| Goals | You should:
|
VMware secures highly privileged access to the Workspace ONE services through a layered defense model that requires strong authentication prior to performing service management functions: Personnel must use VMware-owned equipment when accessing production environment systems. VMware centrally manages patching, anti-virus (AV), and data loss prevention (DLP) software on corporate endpoints through Workspace ONE as our internal end user device (EUD) management platform.
Access to VMware cloud environments is restricted to approved employees with MFA. Employees are prohibited from transferring customer data from the production environment: All access is logged and monitored. VMware Cloud Operations personnel use separate user accounts for administration and normal user activities. Note that customer administrators access and manage the Workspace ONE platform from web-based consoles and do not directly manage the Cloud environment.
- Workspace ONE UEM and Workspace ONE Assist production environment access requires a VPN and jump server.
- Workspace ONE Intelligence leverages secure shell (SSH) access, IP source allow listing, and jump servers for management access to the AWS environment, production app servers and databases.
- Workspace ONE Access/Workspace ONE Hub Services leverage a direct service administration model in which corporate endpoints are used to securely connect to the Workspace ONE Access cloud-delivered services via VPN tied to MFA.
13. Audit information for users
Table 26: NCSC Guidance for audit information for users
| NCSC Guidance | |
| Principle | You should be provided with the audit records needed to monitor access to your service and the data held within it. The type of audit information available to you will have a direct impact on your ability to detect and respond to inappropriate or malicious activity within reasonable timescales. |
| Goals | You should be:
|
VMware Managed Systems
VMware has security controls in place to reduce the risk of unauthorized access to sensitive information in the production environment. Workspace ONE cloud environments intrusion detection mechanisms in place. The services continuously collect and monitor the environment logs which are correlated with both public and private threat feeds to spot suspicious and unusual activities.
VMware has a formal Security Incident Response team that facilitates all Incident Response activities that complies with industry standards for legally admissible chain of custody management processes and controls. VMware has a formal Incident Response team that facilitates all Incident Response activities which uses legally admissible forensic data collection and analysis techniques. Customers can request access to restricted audit data through the VMware Customer Connect or My Workspace ONE support ticketing systems.
Application Logging
Workspace ONE application logs are retained for approximately 30 days for Workspace ONE UEM, Workspace ONE Access and Workspace ONE Assist. Workspace ONE Intelligence keeps historical data for customer trend analysis.
- Workspace ONE administrators can review the integrated application event logs across interactive dashboards and built-in reporting. Leverage advanced and customizable reporting features through Workspace ONE Intelligence.
- Workspace ONE Intelligence gives admins the ability to view and create dashboards around any KPIs across apps, devices, users, and OS updates. Workspace ONE Intelligence offers templates, but administrators can also customize KPIs to meet their specific needs. Admins can resize and move these widgets around the dashboard as they choose.
- The Workspace ONE Access admin console provides audit event reports for resource entitlements for groups and users: Audit events include time, date, and identity of administrative changes to permissions and app access.
14. Secure use of the service
Table 27: NCSC Guidance for secure use of the service
| NCSC Guidance | |
| Principle | The security of cloud services and the data held within them can be undermined if you use the service poorly. Consequently, you will have certain responsibilities when using the service in order for your data to be adequately protected. |
| Goals | You:
|
Customers deployed in VMware cloud environments benefit from managed infrastructure. Customers manage users, data, and configurations associated with the Workspace ONE platform, as well as on-premises connectors (such as VMware Tunnel) and integration points. VMware clearly outlines shared responsibilities with clients the VMware Cloud Services Guide.
Note: Note that roles and responsibilities for products and services licensed through partners may differ depending on the purchasing model.
Workspace ONE includes built-in wizards, such as a tailored Getting Started and Directory Services wizards, to guide the set-up process. The Getting Started Wizard includes enhanced tutorials on Mobile Single Sign-On, Office 365 and configuration chains for devices, content, and applications.
- Keep devices configured to best practices against industry-recommended settings and configurations, such as CIS Benchmarks for Windows 10 with Workspace ONE UEM. Workspace ONE UEM curates these best practices into configurations called Baselines. Customers can also create custom Baselines from ADMX templates.
- Leverage Industry Templates, configuration wizards that enable administrators to deploy recommended industry-specific applications and policies for iOS devices.
Privacy Controls
Workspace ONE UEM enables administrators to customize data collection and view according to privacy and data security needs. For Workspace ONE UEM configure Collect and Display, Collect Do Not Display, and Do Not Collect settings for GPS, Applications, Profiles, and Network data. Customer administrators can choose whether to Display or to Do Not Display end user first name, last name, phone number, email accounts, and usernames within the Workspace ONE UEM console.
Note: Refer to Privacy Best Practices on VMware Docs for additional information.
Customer administrators can require user accept assigned Terms of Use prior to enrollment or accessing enterprise resources.
Workspace ONE Assist provides the ability to accept, pause, and end a remote session at any time, for enhanced privacy.
Documentation
Access a comprehensive and easily accessible catalog of training resources on VMware Docs, My Workspace ONE, and VMware Knowledgebase which provides varying levels of product knowledge and technical expertise, depending on the administrator role.
VMware publishes a campaign kit includes several tools that are pre-designed, pre-written, or pre-planned guide administrators through Workspace ONE Bring Your Own Device (BYOD) adoption. This kit walks IT through exactly how to get started, a sample two-month campaign, who to work with, and tips and tricks to help ensure a successful rollout.
Note: See the BYOD Adoption Kit Assets published on VMware Knowledge Base for pre-designed and pre-written campaign material.
Training
After implementation, access self-guided training resources including product documents, instructional videos, and our knowledge base – all available 24/7.
- Product Documents – Getting started articles, configuration guides, and technical whitepapers that cover key topics and address common challenges.
- Instructional Videos – Our video library consists of succinct instructional videos organized by training curriculum, topic, and experience level to help you manage your own training schedule.
- Knowledge Base – Access valuable tips and tricks written by product experts, product documents, and the latest webinars and announcements.
Customers can also leverage VMware Education Services for training and certification programs designed to grow our customers’ skills and validate their ability to leverage all the opportunities made possible by VMware solutions.
Summary and Additional Resources
This whitepaper documents alignment with the 14 NCSC Cloud Security Principles for Workspace ONE cloud services. The NCSC describes a comprehensive cloud information security program to help enable organizations meet compliance and security obligations within the UK.
Additional Resources
For more information about Workspace ONE Cloud Services, you can explore the following resources:
- Workspace ONE UEM Architecture
- Workspace ONE Access Architecture
- Workspace ONE Intelligence Architecture
- Workspace ONE Cloud Services Security
Changelog
The following updates were made to this guide:
| Date | Description of Changes |
| 2022‑10‑17 |
|
About the Author and Contributors
This document was authored by Andrea Smith, Program Manager, EUC Security and Compliance Assurance.
The following people also contributed their knowledge and assistance with this document:
- Kevin Shaw, Program Manager, EUC Security and Compliance Assurance, VMware
- Stephanie Specht, Program Manager, EUC Security and Compliance Assurance, VMware
- Subha Ramachandran, Program Manager, EUC Security and Compliance Assurance, VMware
Feedback
Your feedback is valuable.
To comment on this paper, contact VMware End-User-Computing Technical Marketing at euc_tech_content_feedback@vmware.com.
