Delivering VMware Anywhere Workspace with DoD365 Integration
Overview
Introduction
In today’s remote worker environment, the Department of Defense (DoD) is migrating away from the COVID-19 emergency response deployment, under the Commercial Virtual Remote (CVR) program. The solution was invoked at the time to ensure a rapid enablement of the remote worker within the DoD branches/services access to Microsoft’s commercial O365. Now, a transition to a higher security, long-term office productivity environment that end-users will leverage both in the office and at home has begun. This transition involves connecting to a DoD-enhanced version ‘DoD365’, as well as other derivatives that are custom to military branches (e.g., Army365).
However, numerous complexities with the deployment will make a single, scalable solution challenging to leverage as a sole-source set of enablement solutions, especially when coupled with a growing list of the DoD’s plans for device and end-user enablement options, such as the decision to allow personnel to access its new collaboration platform DoD365 with personal devices (BYOD), beyond the government-provided (i.e. Government-Furnished Equipment (GFE)) mobile devices would be allowed to connect to the service and remote enablement.
When taking in the sheer scale of these enhancements, it’s important to consider how the VMware Workspace ONE® suite and its integration with Microsoft 365 (M365) implementations in the Federal Government, and specifically the DoD, provide a true multi-cloud approach and support an evolution beyond CVR and provide a digital transformation of remote work enablement via VMware Anywhere Workspace.
Audience
This document is intended for IT administrators and product evaluators who are familiar with VMware's Anywhere Workspace powered by EUC and VMware Workspace ONE. Familiarity with the End-User Computing environment and modern management that include device, app and identity management is assumed. Knowledge of other technologies, such as VMware Horizon, Security, Secure Access Service Edge (SASE), and Zero Trust Architecture (ZTA) is also helpful.
Enablement
Anywhere Workspace, powered by the Workspace ONE End-User Computing (EUC) suite, provides the necessary enablement of DoD365 integration and enhancements for enterprise-grade UEM, cloud-enablement, and cybersecurity elements for Zero-Trust Security, including:
- Enterprise IT-as-a-Service (EITaaS) - Enterprise service enablement & acceleration through centralized IT features & staff support, powered by VMware Workspace ONE.
- App Modernization & Management - Access to data and info in centralized data lakes
- Multi Cloud Integration - FedRAMP-hosted / On-Prem / milCloud / Hybrid Cloud (HCX) and cloud independent, e.g., VMware / AWS / Azure / Private and so on.
- Virtual Cloud Networking (VCN) - Integration with VMware VCN or 3rd party versions.
- Virtual Desktop Interface (VDI) - Enable remote desktop access and security.
- Zero-Trust Security (ZTS) - Aligned to endpoint security, as well as the network and communications via Secure Access Service Edge (SASE).
- Command & Control (C2) - Easy integration and management controls & automation.
Solution
The Workspace ONE suite and its components help with this large-scale, enterprise transformation and the integration with DoD365; its components provide the flexibility and scalability needed to make the transition, including:
- Workspace ONE Unified Endpoint Management (UEM) for Mobile Device Management (MDM) and policy enforcement and access controls for modern management of a blended end-user deployment spanning Win 10/macOS/iOS/Android and Linux based devices.
- Workspace ONE Access for Identity and Configuration and Access Management (IdM/ICAM) providing for mobile authentication and digital signing with Derived Credentials and certificate-based authentication (CBA).
- Workspace ONE Intelligent Hub services for Content, Application and Training Management and Enablement and User Experience (UX), including App Catalog and Self-Service.
- Workspace ONE Boxer secure, National Information Assurance Partnership (NIAP) compliant, email client with data loss prevention (DLP).
- Workspace ONE Tunnel for a per-app virtual private network (VPN), providing secure in-transit communications.
- Workspace ONE Intelligence to correlate data from multiple sources for visibility and automated workflows.
- Workspace ONE Horizon providing for secure delivery of virtual desktop interfaces (VDI) and apps across hybrid cloud, from a single control plane with rapid provisioning, automation, and simplified management to extend the best digital workspace experience to end-users.
Each of these elements provide a DoD entity the ability to take on the tasks of modern CVR transition engagements that will be required of a true enterprise-grade ‘Remote Access’ for DoD-based personnel to M365/DoD365 collaboration utilities such as MS Teams, integration to .mil E-Mail and data and file-sharing tools, including SharePoint.

Figure 1: EUC Portfolio Logical View for Anywhere Workspace
Advantages and Drivers
There are several reasons that VMware customers have moved away from legacy device administration & deployment utilities as quickly as possible. The key motivation for this can be summarized by the following points and key Workspace ONE deployment drivers not only in commercial but specifically in the FedGov and DoD space:
- Modern Management for Policies – VMware UEM can navigate around the pitfalls of pre-defined settings and a lack of dynamic, custom settings, including providing for a full User Interface (UI), as well as traditional Group Policy Object (GPO) support, that can be used Over-the-Air (OTA), without VPN connectivity, and configure Cloud-based GPOs leveraging a service provider, baseline templates or a policy builder that helps create custom policies, as well as supporting the use of a 3rd party Administrative Template XML-Based(ADMX) file for policy settings in GPO for Windows; additional VMware UEM services, such as VMware Workspace ONE Airlift can help further in analyzing, planning, and migrating to cloud-based GPOs.
- Multi-tenancy – ability to manage multiple domains and deployment environments within one ‘pane-of-glass’ through Workspace ONE UEM.
- Automation, On-boarding & Provisioning – ability to leverage Apple DEP / ABM or Google auto-provisioning, as well as other vendor programs and the inclusion of self-provisioning services and to the enroll / de-enroll process be automated after HR-based actions and perform granular enterprise task and features, such as print server configs.
- Role-Based Access Controls (RBAC) - for numerous, divergent support groups and admin levels, including the ability to obfuscate Personally Identifiable Information (PII) at an individual admin level, that go far beyond ‘scope-tags’ and provides for true ‘delegated administration’ amongst disparate teams/groups and ‘granular’ protected views and segmented admin views.
- Conditional Access – true vendor-independent, app access & management; not specific to only Microsoft-based apps but can be leveraged across the platform spectrum for providing device posture and behavioral risk paramount to providing Zero-Trust Security device and other enhanced security options for a more complete contextual compliance assurance for access to those apps & data with explicit ability to perform tasks, such as quarantining a device that has a known vulnerability for a specific group of users, for a specific non-Microsoft app e.g., Box version X.Y and for XYZ category of users or an X group.
- API / Device Integration – larger pool for greater device portfolio and easier integration with Workspace ONE; includes ruggedized Android-based (e.g., Zebra-based for Healthcare) or other OS's such as Chrome OS for a greater security framework and compliance posture for Endpoint Detection / Response, including automation.
- Device Log Views - ability to view them on a ‘per-device’ level, in order to perform Incident Response at a device level for better granular troubleshooting and Endpoint Detection & Response/Incident Response (EDR/IR).
- Compliance Reporting - more accurate, robust & up-to-date device and app-level details for compliance validation for organizations.
- Data encryption & Data Loss Prevention (DLP) – on the device (e.g. passcode based) and in-Transit (e.g. Per-app), as well as through a ‘VMware Tunnel’ if needed for high security of all traffic through a VPN gateway on all apps; not just Microsoft-based, ensuring full-scope DLP, including solution specific VPN client tunnels, built-in secure content locker application and ability to enforce E-Mail compliance and enable pdf signing capabilities.
- Identity Provider (IdP) – integration is provided via a large ecosystem of 3rd party solution providers of Identity Management (IdM), and as Cloud Service Providers or IdM-as-a-Service (IDaaS), including Okta, Ping or native IaaS solutions of Azure / AWS / Google.
- Public Key Infrastructure (PKI) Lifecycle Management - ability to properly transition between cert renewals without having to republish profiles/apps as well as, perform more than just add/revoke for Certificate-based Authentication (CBA). Also, can be used to authenticate within apps, which can have privacy data (e.g., Teams) contained within them; includes Multi-factor Authentication (MFA), risk-based, and Derived Credentials integration options (e.g., Purebred) for both iOS & Android devices.

Figure 2: Workspace ONE PIV-D Manager interacts with Purebred derived credential (DC) or other providers & the Workspace ONE UEM components
- Policy Processing – ability to provide expeditious and rapid, enterprise-grade policy processing, at speeds that don’t take hours to target policies that are grouped together, keeping backlogs at a minimum for things such as, auto-lock / log-off screen / remote lock controls, which can be enabled in conjunction with FISMA / STIG controls.
- Audit Logs & Tracking – directly available from within the console and available integration with Trust Partner Network providers for Security Information & Event Management (SIEM) and ability to enable specific communication/alerts for notification of incidents to relevant parties (e.g., SecOps).
- Training Curriculum Management – delivery and portal experience of soldier and agent training run from within Intelligent Hub to help track compliance.
Key Differentiators
As part of the solution, including the VMware Application & Desktop Virtualization Horizon (VDI) solution which integrates with Azure AD (AAD), Workspace ONE serves as the foundation to deliver Enterprise IT-as-a-Service (EITaaS), while enabling Zero Trust initiatives throughout the DoD, including integrated Trust Partners for additional-layered cybersecurity of endpoints (e.g., Mobile Threat Defense (MTD)).
Other key things that distinguish VMware Workspace ONE:
- FedRAMP Authorized SaaS – unique GSA FedRAMP authorization for the Workspace ONE: UEM, Access, Intel Hub, Intelligence & Software-as-a-Service (SaaS), outside of an Infrastructure-as-a-Service (IaaS) set of internal / embedded services.
- National Information Assurance Partnership (NIAP) certified email client (e.g. VMware Boxer) and MDM (VMware Workspace ONE UEM), that provide the only UEM feature suite that can be used and deployed in all three environments e.g. Private or Public Cloud <and> On-Premise, as well as in a VMware-Hosted FedRAMP Authorized SaaS version.
- Commercial Solutions for Classified (CSfC) from the National Security Agency (NSA) provides for a mobility capability package that is supported by NIAP and the VMware solution suite meets the requirements necessary to provide services in each of those categories for classified mobile communications listed previously.
- Security Technical Implementation Guide (STIG) compliance with security controls set forth specifically within the MDM & Mobility Deployment Services for OnPrem EUC functions, as well as a robust set of server and virtualization product areas as well.
- DoDIN APL for DoD branches/agencies; only vendor for use in the Multifunction Mobile Device Backend Support System (MBSS) a.k.a. UEM-based suite of services.
- NIST SP 800-207 Zero Trust Architecture (ZTA) guidance for emerging compliance areas of Cybersecurity, including being FirstNet Listed for 1st responders by the FirstNet Authority for Mobile Device Management solution for both iOS & Android.

Figure 3: Zero Trust Journey and inclusion of EUC/Anywhere Workspace User Access Model for ZTA
- Cybersecurity Maturity Model Certification (CMMC) Lifecycle management and security compliance is provided by the VMware Workspace ONE EUC suite to enable contractors, Service Providers (SPs) under the DoD’s own ability to help customers meet those requirements and to enable a secure deployment for those controls.
- AppConfig Community is an industry-based consortium that VMware is a proud member of, which provides guidance from the industry vendors themselves, for the development, deployment, and use models for UEM/MDM integration with secure mobile apps.
- Third-Party Trust Network provides a robust ecosystem of solution integration with Carbon Black for Endpoint Protection, as well as Mobile Threat Defense solutions (e.g., Lookout) <and> in order to integrate the data collection of these utilities into VMware’s FedRAMP Authorized Workspace ONE Intelligence service for enhanced 'Incident Response' capabilities on all device types e.g. macOS / Win10 / mobile / Rugged, as well as Security Information & Event Management (SIEM) integration (e.g., Splunk) and other Technical Alliance Partner(s).

Figure 4: Logical Connections & Service Integration to DoD365 with VMware EUC Components and ZT baseline
Architecture and Deployment Considerations
To properly provide the DoD with the capabilities required of the NexGen version of CVR, it’s important to ensure that all the use cases for this integration environment are addressed and the flexibility of that integration is available regarding solution environment and end-user support between Government-Furnished Equipment or Bring Your Own Device – Approved Devices (BYODAD)-based devices and their users in multiple scenarios including:
- Service hosting environments > On-Premises; Private/ Public/ FedRAMP & Hybrid (HCX) Clouds
- End-user options > GFE / BYODAD-Managed/ BYODAD-Unmanaged (a.k.a. Registered Mode)
Only VMware Workspace ONE can enable the differing hosting environments and end-user/device use cases!
Note: See the Additional Resources section for detailed information about the solution deployment options and the technologies behind them. Regarding future deployment guides & tutorials, new assets will be coming this summer related to Anywhere Workspace and Workspace ONE and DoD365 Integration; refer to VMware Tech Zone.
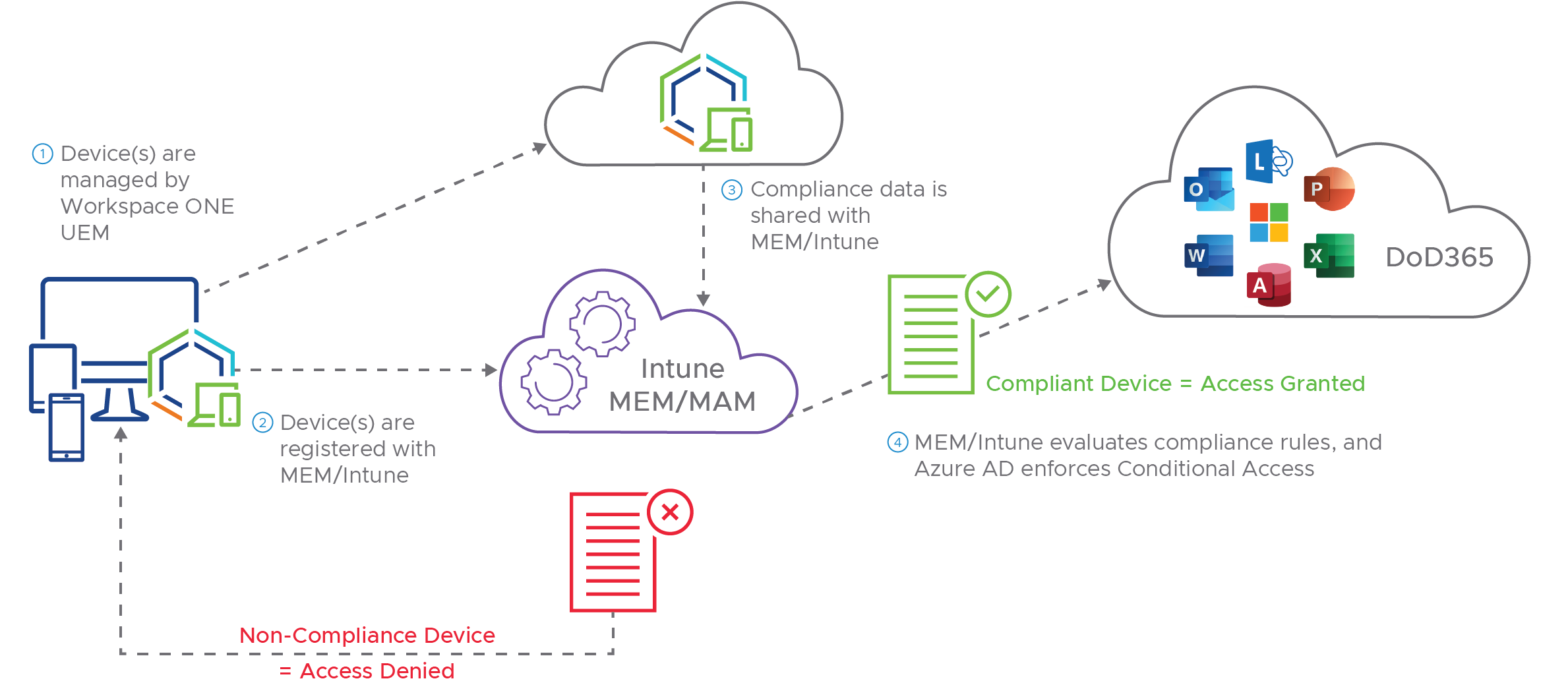
Figure 5: VMware UEM logical view of authentication flows with DoD365
Compliance
Also, these tools help branches and agencies to meet compliance and implement security control requirements for not only previous frameworks, such as NIST 800-53 FISMA but also leverage accredited solutions under National Information Assurance Partnership (NIAP) while providing compliance with security controls set forth specifically within the Defense Information Systems Agency (DISA) Security Technical Implementation Guide (STIG), as well as emerging compliance areas of Cybersecurity within the NIST SP 800-207 Zero Trust Architecture (ZTA) guidance, as well as Lifecycle management and security compliance under the DoD’s own Cybersecurity Maturity Model Certification (CMMC) and VMware’s ability to help customers meet those requirements and to enable a secure deployment for those controls.
The Workspace ONE solution suite will support an ‘Anywhere Workforce’, including GFE / BYO Approved Devices (BYOAD) while providing an enhanced ‘service scalability’ not found in other platforms in the UEM space. Also, integrated VMware tools within EUC, such as VMware Workspace ONE® Assist™ to remotely access and troubleshoot devices in real-time.
Summary and Additional Resources
Introduction
As the DoD’s remote worker footprint continues to grow, including on the heels of recent DoD announcements for allowing DoD365 to be reached through personal cellphones/devices (e.g. BYOD), it will be even more important to ensure that enterprise-grade Unified Endpoint Management (UEM) and Cybersecurity management and protection solutions are embedded with the DoD365 integration service. These are solely met within the VMware Anywhere Workspace for DoD365 Integrated solution and removes the need to compromise to only receive the bare-minimum options for those necessary tools IT and the organization requires for an enterprise-grade set of utilities that support those use-cases for the DoD.
Workspace ONE is more than just a set of management tools for IT and Mobility admins. Rather, it’s a NexGen solution geared to enable the transformative move to a true ‘Anywhere Workspace’ and digital enablement for remote and local workers within an agency that doesn’t rely on additional contract features/layers to enable the services needed to do the job or hide the true deployment and operational costs. Workspace ONE is a digital platform that delivers any app, on any device to any worker with intrinsic security and compliance embedded within it and reduction in complexity and management.
Outcomes
VMware Workspace ONE Integration with DoD365 provides a better solution and experience for both end-users, IT administration staff, as well as management, including:
Table 1: Outcome Matrix for VMware EUC suite and UEM integration with DoD365
| IT Transformation |
|
IT modernization – remove technical and process debt Remove hidden Ops & Support costs and the complexity of third-party tools Faster time to value realization – deliver technical outcomes quickly |
| Faster Device Compliance |
|
Profile and application delivery is near-instantaneous with Workspace ONE, reducing risk present vs. Intune that can take up to 8 hours to process and reconcile |
| Less administrative overhead |
|
Automated support and management tasks, ensuring key apps are installed in order to maintain device compliance policy options |
| Faster support |
|
Remote Assist speeds up time-to-issue resolution |
| Operational efficiencies |
|
Reduced run costs and increased organizational efficiency |
Additional Resources
For Microsoft O365 reference material, see the following:
- TechZone: Understanding MS O365 Integration
- TechZone: Managing Win10 Updates with WS1
- Docs: Workspace ONE PIV-D Manager & Supported Derived Credentials
For Workspace ONE & Anywhere Workspace Technical Solution Documentation, see the following:
- Docs: WSO Suite Solution Guide
- TechZone: UEM Reference Architecture
- TechZone: WSO Mobile App Mgt
- Docs: Intelligence Product Guide
- Docs: Intelligent Hub Services
- Docs: Horizon VDI
- TechZone: WSO UEM Architecture
- TechZone: WSO Access Architecture
- Docs: Release Notes for WSO Intelligent Hub
- TechZone: WSO Intelligence Architecture
- TechZone: WSO Horizon Architecture
- TechZone: Deploying Unified Access Gateway for Horizon VDI
- TechZone: Service Integration for EMM Services for Horizon VDI
For supporting documentation on Cybersecurity, see the following:
- VMware Zero Trust Security Workspace ONE Whitepaper
- Zero Trust Secure Access to Traditional Applications with VMware
- TechZone: Vetting 2fA with Universal Broker for VMware Horizon VDI
- TechZone: WS1 Access: Config with 3rd Party IdP Video
- TechZone: WS1 Access Policies for Zero Trust and Conditional Access Video
- TechZone: Practical Guide to Implementing Zero Trust Video
- TechZone: Cloud Delivered Enterprise Remote Access & Zero Trust Video
For solution analysis, comparison and costing, see the following:
- TechZone: Business Drivers & Use-cases for Reduced Support Calls & Improved Time-to Resolution
- Forrester Report: Total Economic Impact Study on Win10 Mgt
- IDC Report: Business Value of Running Apps on VMware Cloud
- Gartner Report: Magic Quadrant for Unified Endpoint Management (August 2020)
- Gartner Report: Critical Capabilities for Unified Endpoint Management Tools (August 2020)
- The Forrester New Wave: End-User Experience Management, Q4 2020
- Forrester New Wave Report: Spotlight: How to Get to From Here to Zero Trust (October 2020)
- IDC MarketScape: Worldwide Unified Endpoint Management Software 2021 Vendor Assessment
Additional Certifications and Compliance
VMware is committed to supporting government IT programs and the extended ecosystem/supply chain worldwide and we continue to expand our compliance programs to meet the requirements of the most demanding missions.
For more information on VMware Federal Certifications & compliance, see the following unique listings for other global and governmental focused compliance, see the following:
- VMware's NCSC 14 Cloud Security Principles Guide – Nat'l Cyber Security Centre (NCSC) for EU framework and General Data Protection Regulation (GDPR) guidance
- VMware's Workspace ONE Cloud Services – ISO’s 27001, 27017 & 27018 Certifications
Changelog
The following updates were made to this guide:
|
Date |
Description of Changes |
|
2021/06/29 |
|
About the Author
Andrew Osborn is serving in a role at VMware as a dedicated ‘Staff Technical Marketing Architect’ for all things End-User Computing (EUC) compliance / regulatory. He has over 20 years’ experience in the IT Industry, including the last 8 years within Public Sector, with roles spanning Cybersecurity, Networking, Enterprise Ops, Mobility & Telco solutions, encompassing numerous technologies and architectures. Andrew received an MIS degree from University of Oklahoma with certs from ISC2 CISSP & GIAC GSLC and is based out of San Antonio, TX. He'll be contributing to VMware’s Tech Zone to provide more tailored messaging for Federal, State, Local & Education (SLED) solutions from VMware EUC.
Feedback
Your feedback is valuable.
To comment on this paper, contact VMware End-User-Computing Technical Marketing at euc_tech_content_feedback@vmware.com.
