Best Practices for Managing Microsoft BitLocker with Workspace ONE UEM
Overview
VMware Workspace ONE® UEM provides administrators with the ability to configure BitLocker encryption on managed Windows Desktop devices. Using the Encryption profile, administrators can set native BitLocker encryption policies to ensure data remains secure, while recovery keys are created and stored within the Workspace ONE UEM console, and accessible through the self-service portal. Workspace ONE UEM also allows for the configuration of BitLocker To Go, a drive encryption technology on removable data drives.
What Is BitLocker Encryption?
Microsoft BitLocker is a volume encryption feature first introduced with Windows Vista and has since become an integral part of the security baseline for many commercial and enterprise organizations. Designed to address data loss from stolen, lost or improperly decommissioned computers, BitLocker provides data encryption for operating system and fixed data volumes.
BitLocker can use the following encryption methods:
- AES CBC 128-bit
- AES CBC 256-bit
- XTS AES 128-bit
- XTS AES 256-bit
For more information, see Microsoft Docs: BitLocker Overview.
What is BitLocker To Go?
BitLocker To Go (BL2Go) is a Windows tool that encrypts removable data drives to prevent unauthorized access. BL2Go can use a password, smart card, or a recovery key to decrypt removeable devices, such as:
- USB flash drives
- SD cards
- External hard disk drives
BL2Go can encrypt removable data devices that are formatted using the following file systems:
- NTFS
- FAT32
- FAT16
- exFAT
For more information, see Microsoft Docs: BitLocker To Go FAQ.
Workspace ONE UEM Encryption Profiles for Windows Desktop
Workspace ONE UEM provides a comprehensive set of options for deploying and managing BitLocker on a Windows Desktop device. These options allow administrators to secure devices using native BitLocker encryption. The following settings are available in the encryption payload.
Table 1: Workspace ONE UEM Encryption Profile Settings
| Settings | Description |
| Encrypted Volume | Workspace ONE UEM gives you the option to encrypt all hard disks on the device, or only the system partition. See Configure Hard Drives as a Single Volume Rather than Multiple Volumes for OS and Data for recommendations related to this setting. |
| Encryption Method | This setting identifies the method to be used at the time the hard disk(s) are encrypted. The available options are:
The Default option will use the default encryption method specified by the OEM. |
| Only Encrypt Used Space During Initial Encryption | When this option is selected, BitLocker will only encrypt used space on the hard disk at the time of encryption. |
| Custom URL for Recovery Key | You can specify the URL used by end users to get the recovery key for their device. Because Workspace ONE UEM hosts the recovery keys in the Self-Service Portal, you should consider using that as the URL. |
| Force Encryption | This option will force re-encryption of the device if BitLocker is manually deactivated. See Carefully Consider Options Such as Force Encryption and Always Keep System Encrypted for recommendations on the use of this setting. |
| Keep System Encrypted at All Times | When selected, this option ensures that the device remains encrypted, even during device wipes, profile removals, or disconnects from Workspace ONE UEM. See Carefully Consider Options Such as Force Encryption and Always Keep System Encrypted for recommendations on the use of this setting. |
| BitLocker Authentication Settings: Authentication Mode | End users must authenticate before accessing an encrypted device. This option allows you to select the authentication method to be used. The methods available are:
See Use TPM Instead of Password Protectors for recommendations on this setting. |
| BitLocker Authentication Settings: Require PIN at startup | When selected, this option requires the user to enter a PIN prior to operating system start up or auto-resume from suspend or hibernate mode. |
| BitLocker Authentication Settings: PIN Length | Use this option to specify the required length of the startup PIN. By default, the PIN will be numeric. If additional complexity is required for the PIN, you can configure Allow Enhanced PIN at Startup. |
| BitLocker Authentication Settings: Allow Enhanced PIN at Startup | If you require a more complex PIN, select this option to activate the use of uppercase and lowercase letters, symbols, numbers, and spaces. |
| BitLocker Authentication Settings: Use Password if TPM Not Present | This option will allow a password to decrypt the device if TPM is unavailable. |
| BitLocker Authentication Settings: Suspend BitLocker until TPM is initialized | This option will postpone the encryption of a device until TPM is initialized, which can be useful for Out-of-Box Experience (OOBE) enrollments. |
| BitLocker Authentication Settings: Minimum Password Length | Use this option to set the minimum number of required characters for a password. |
| BitLocker Static Recovery Key Settings: Create Static BitLocker Key | This option activates a static recovery key that is shared across a group of devices. |
| BitLocker Static Recovery Key Settings: BitLocker Recovery Password | Click the Generate icon to create a new recovery key. |
| BitLocker Static Recovery Key Settings: Rotation Period | Use this option to specify the number of days for recovery key rotation. |
| BitLocker Static Recovery Key Settings: Grace Period | This option configures the number of days that the previous recovery key will continue to work after rotation. |
| BitLocker Suspend: Activate BitLocker Suspend | The setting activates BitLocker Suspension, which suspends BitLocker encryption during specified times such as scheduled updates. BitLocker Suspension allows the device to reboot without the need for an encryption PIN or password. |
| BitLocker Suspend: Suspend BitLocker Type | With this option, you can select to either activate BitLocker Suspension on a recurring schedule or specify a Custom day and time. |
| BitLocker Suspend: BitLocker Suspend Start Time | This option allows you to specify the start time for BitLocker Suspend. |
| BitLocker Suspend: BitLocker Suspend End Time | Use this option to specify an end time for BitLocker Suspend. |
| BitLocker Suspend: Scheduled Repeat Type | With this option, you can set the type of recurrence for BitLocker Suspend. You select daily or weekly. |
Purpose of This Tutorial
The purpose of this guide is to provide recommendations and considerations for how to best configure BitLocker settings and policies on Windows Desktop devices managed by Workspace ONE UEM. The best practices outlined in this document are based on customer experiences and engineering feedback.
Audience
This guide is intended for IT professionals and Workspace ONE UEM administrators of existing production environments who manage Windows Desktop devices with Intelligent Hub.
Knowledge of additional technologies such as encryption, Windows Desktop device management, and VMware Workspace ONE® UEM is also helpful.
Best Practices and Considerations
The following items should be considered before creating and configuring an encryption profile for Windows Desktop devices in Workspace ONE UEM.
Use TPM Instead of Password Protectors
Although BitLocker can encrypt the Windows operating system on a computer that does not have a Trusted Platform Module (TPM) version 1.2 or later, it is recommended that TPM be used whenever possible. With the release of Windows 8, BitLocker can provide protection to the operating system volume on a computer without TPM by using either a USB startup key or an operating system volume password. However, neither of these options can provide system integrity verification at pre-startup that BitLocker can offer when TPM is present in the system. Setting TPM as the authentication mode for BitLocker will provide the most secure option for device encryption.
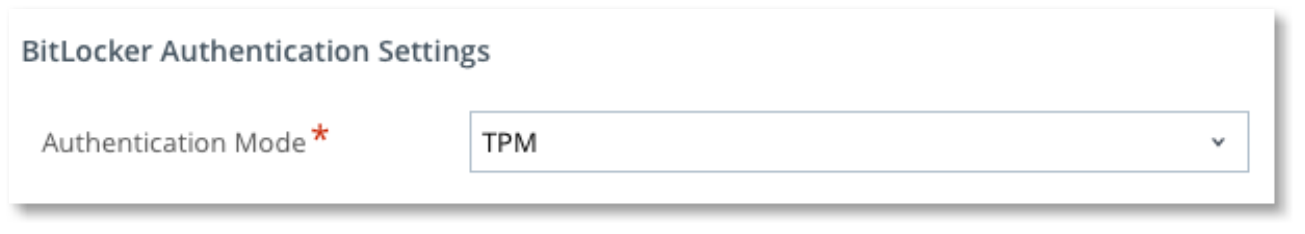
Figure 1: BitLocker Authentication Mode in Workspace ONE UEM
Configure Hard Drives as a Single Volume Rather than Multiple Volumes for OS and Data
When Workspace ONE UEM sends a BitLocker Profile to a computer with multiple volumes, the operating system partition is assigned a newly created numerical protector, and the additional volumes are assigned Auto Unlock protectors that will unlock the volumes with the OS volume. Although Workspace ONE UEM maintains recovery keys for all hard drives, the recovery of multiple logical volumes on a single hard disk can create additional complexities. Whenever possible, it is recommended that you configure a single volume per hard disk for OS, applications, and data.
Allow Workspace ONE UEM to Manage the Full BitLocker Lifecycle
Microsoft offers several mechanisms for enabling and managing BitLocker on computers, including Microsoft Intune, Endpoint Configuration Manager, and Microsoft BitLocker Administration and Monitoring (MBAM). Creating a device profile in Workspace ONE UEM to activate BitLocker is the recommended mechanism for managed Windows Desktop devices. The recommendation includes enrolling the device in Workspace ONE UEM prior to enabling BitLocker and allowing UEM to manage BitLocker settings. Unintended complexities and issues can occur if BitLocker GPO settings, other management tools, or manual enablement are introduced into the environment.
If a BitLocker encrypted Windows Desktop device is enrolled in Workspace ONE UEM and a device profile to manage BitLocker is applied, the new UEM specific protectors are added to the existing protectors. If the encryption profile is removed, all protectors will be removed from the device.
Some situations exist where existing protectors cannot be used with Workspace ONE UEM, such as password protectors on an operating system volume.
Considering these potential additional complexities, it is recommended that the full lifecycle of BitLocker be managed through Workspace ONE UEM, including profile install, encryption, management, and decryption on decommission.
Avoid End User Pre-Encryption Prior to Enrollment
End users can activate BitLocker on their device through the Control Panel applet in Windows. As mentioned earlier, pre-enrollment BitLocker encryption can introduce issues after a device in enrolled in Workspace ONE UEM, and a BitLocker device profile is applied. It is best to avoid any pre-enrollment BitLocker encryption and allow Workspace ONE UEM to manage the entire BitLocker lifecycle.
When Removing Encryption Profiles, Avoid Rebooting the PC Until the Decryption Process is Complete
When an encryption profile is removed from a Workspace ONE UEM managed Windows Desktop device, BitLocker will begin the decryption process of the protected volumes. Prior to the release of version 2206 of the Workspace ONE UEM console, possible data loss could occur if a Windows device was rebooted during the decryption process. In this rare situation, the Auto Unlock protector and numerical password protector were removed from the device when the decryption process started. If the device was rebooted before decryption completed, there would be no active recovery keys available.
A change was introduced in Workspace ONE UEM with version 2206 to maintain the protectors on the device until decryption is complete. However, it is still recommended that the Windows Desktop device is not rebooted until the decryption process finishes. This will ensure the integrity of the data on the volumes being decrypted.
Carefully Consider Options Such as Force Encryption and Always Keep System Encrypted
When activated, the Force Encryption option in BitLocker monitors for attempts to manually deactivate encryption on the Windows Desktop device. Such a status change may occur if the user has administrative privileges on the device and deactivates BitLocker from the Control Panel applet. If a status change is detected, Force Encryption will automatically re-activate encryption. Having this feature activated may create complexity during operations where system processes expect BitLocker to be suspended, such as Basic Input/Output System (BIOS) updates, hardware changes, Windows Updates, and device wipes and resets. Changes have been implemented in version 2206 of Workspace ONE UEM to resolve this issue regarding device wipes. However, prior console and hub version combinations may still be impacted. Users that do not have administrative privileges on the Windows Desktop device do not require Force Encryption activated.
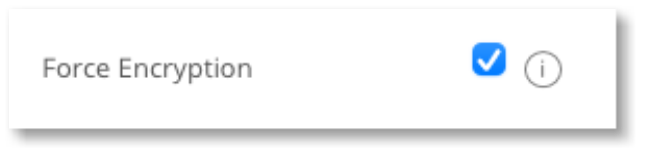
Figure 2: Force Encryption setting in the Encryption Payload
The Always Keep System Encrypted option ensures that the Windows Desktop device remains encrypted if actions occur that remove device profiles, such as wipes and resets, removal of Intelligent Hub, or disconnecting from the work/school account. Any of these events can remove device profiles, including profiles that activate BitLocker. When activated, the Always Keep System Encrypted option will refrain from decrypting the volume and the Workspace ONE UEM console will retain the recovery keys. Although this feature can ensure data security if a device must be wiped due to loss or theft, it can be problematic if Intelligent Hub is intentionally removed for device troubleshooting.
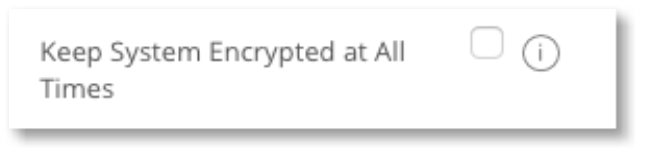
Figure 3: Keep System Encrypted at All Times setting in the Encryption Payload
Use Caution When Using Group Policy to Manage BitLocker on Devices Enrolled in Workspace ONE UEM
BitLocker settings can be managed in several ways, including the use of Active Directory Group Policy (GPO). Workspace ONE UEM device profiles contain a subset of the settings available in Group Policy. When using both Group Policy and device profiles to manage BitLocker, it is possible for GPO settings to be unintentionally overridden by those in Workspace ONE UEM device profiles and vice versa. Potential conflicts between GPOs and device profiles may cause unexpected system behaviors that could impact access to encrypted volumes.
Be aware of the BitLocker configurations in GPOs as well as device profiles and carefully consider the impact of each on the other. This will minimize potential impact caused by conflicting policies.
BitLocker To Go Password Complexity and Minimum Length Requirements are Not Displayed in the Graphical User Interface
BitLocker To Go (BL2Go) provides drive encryption for removable data drives, such as USB flash drives, SD cards, and external hard disk drives. When the BL2Go feature is activated, a password screen appears when a removable drive is attached to the Windows device. The graphical user interface (GUI) for BL2Go indicates that the minimum character requirement for the password is eight (8). The GUI does not, however, indicate if additional complexity or character length requirements have been set through local policy or group policy. This can result in potential user experience issues if additional complexity is required of which the user is unaware.
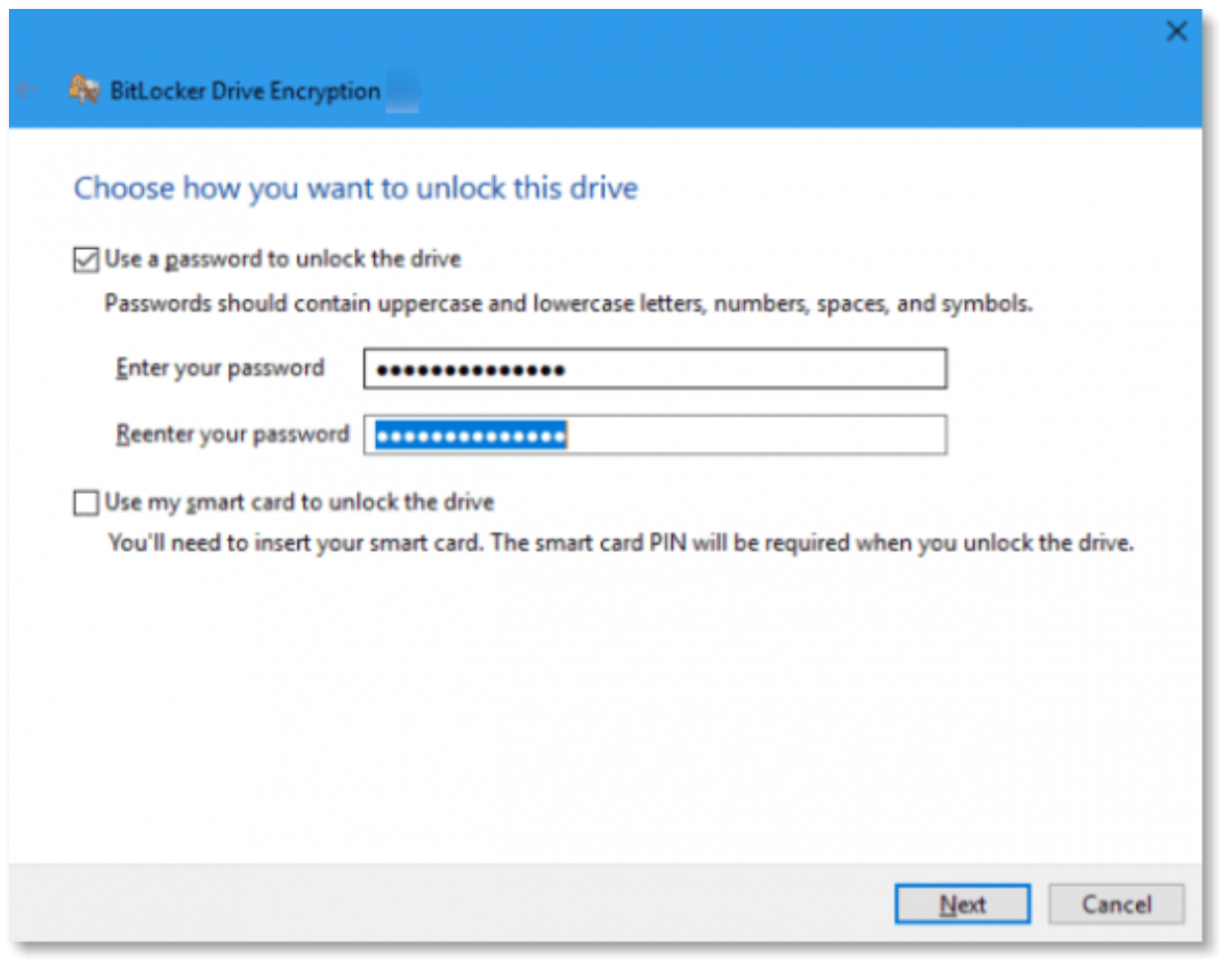
Figure 4: BitLocker to Go password screen
Use Single Use Recovery Keys for BitLocker
Recovery keys for encrypted volumes are stored in the Workspace ONE UEM console and can be accessed through the self-service portal or by contacting the organization’s helpdesk. Because of the static nature of the recovery key, it is possible for a user to save the key and re-use it later to unlock the volume. If the user keeps the key in an unsecure place, such as taped to the bottom of the Windows Desktop device, the device can be compromised if stolen, and information on the volume can be accessed. This can create a significant security vulnerability for an organization. To remediate this security risk, it is recommended that you use Single Use Recovery Keys for BitLocker.
As of Workspace ONE UEM version 2210, you can configure a Single Use Recovery Key for BitLocker. When using the Single Use Recovery Key option, Intelligent Hub detects when a volume is unlocked with a recovery key and generates a new recovery key which it sends back to the Workspace ONE UEM console for safe keeping. This ensures the integrity of the encrypted system by forcing the rotation of the recovery key and ensures that the user cannot re-use the existing recovery key later. The current recovery key remains active on the device until Intelligent Hub can confirm that the Workspace ONE UEM console has received the new recovery key. A successful rotation of the recovery key is noted in the console troubleshooting log allowing administrators to monitor ongoing operations.
Summary and Additional Resources
This tutorial provided several best practices and considerations for managing BitLocker on Windows Desktop devices with Workspace ONE UEM.
The best practices and considerations discussed include:
- Using TPM instead of password protectors for BitLocker encryption
- Configuring hard drives as single volumes rather than multiple volumes for OS and data
- Allowing Workspace ONE UEM to manage the full BitLocker lifecycle
- Avoiding end user pre-encryption prior to device enrollment into Workspace ONE UEM
- Avoiding reboots after device encryption profiles removal until the decryption process completes
- Careful consideration when using options such as Force Encryption and Always Keep System Encrypted
- Being cautious when using Group Policy to manage BitLocker on devices enrolled in Workspace ONE UEM
- Being aware that BitLocker to Go password complexity and minimum length requirements are not displayed in the graphical user interface
- Utilizing Single Use Recovery Keys for BitLocker
For more operational tutorials on Workspace ONE UEM, check out the Digital Workspace Tech Zone.
Additional Resources
For more information about Workspace ONE UEM, you can explore the following resources:
- Enabling BitLocker Encryption to Remote Windows Devices
- VMware Workspace ONE UEM: BitLocker Encryption – Feature Walk-through
- Workspace ONE UEM Production Documentation – Encryption Profile (Windows Desktop)
- VMware Knowledge Base
Changelog
The following updates were made to this guide:
| Date | Description of Changes |
| 2022/10/18 |
|
About the Author and Contributors
This tutorial was written by:
- Michael Bradley, Senior Technical Marketing Architect, End-User-Computing Technical Marketing, VMware.
With significant contribution by:
- Vani Hegde, Senior Product Manager, Windows Management PM, VMware.
- Kevin Sheehan, VMware Alumni.
Feedback
Your feedback is valuable.
To comment on this paper, contact VMware End-User-Computing Technical Marketing at euc_tech_content_feedback@vmware.com.
